What happened, in plain terms that still stay precise
Coruna is not a single iOS bug and it’s not just another “spyware rumor.” What Google’s Threat Intelligence Group actually published is the anatomy of a full exploit kit: five complete exploit chains, 23 exploits total, and an operational framework built to reliably compromise a wide range of iPhone models running iOS 13.0 through iOS 17.2.1. (Nube de Google)
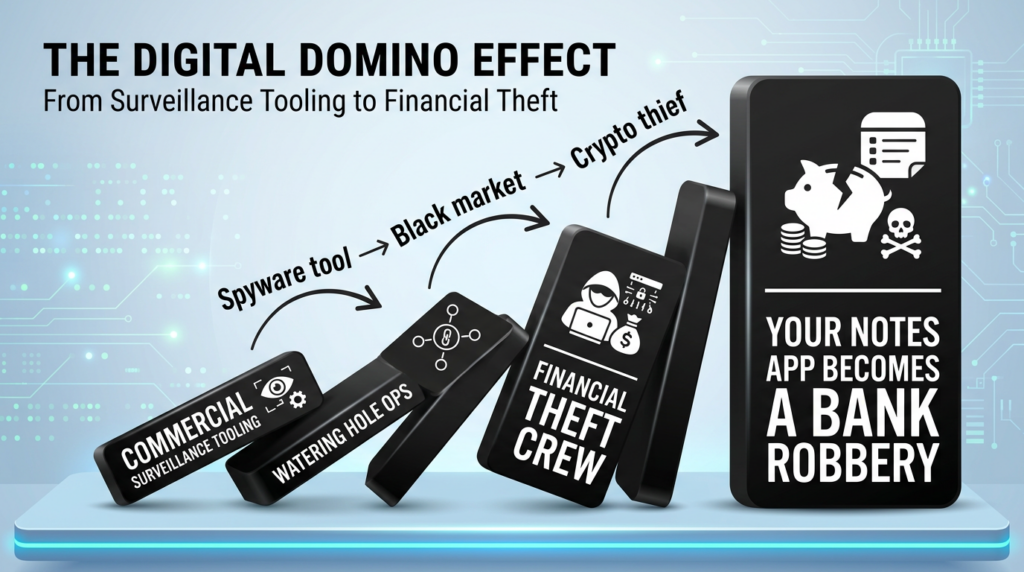
The story becomes more alarming because the kit did not stay inside one actor’s pipeline. Google tracks Coruna across 2025 from a commercial surveillance context, to watering hole attacks targeting Ukrainian users, and later to broad-scale campaigns run by a financially motivated actor operating from China. The key sentence is not “who built it,” but “how widely it traveled,” because once a chain like this is in circulation, every future iOS bug becomes a potential “drop-in replacement” component for the next version of the kit. (Nube de Google)
iVerify’s parallel reporting matters for a different reason. They frame this as the first observed mass exploitation of mobile phones by a criminal group using tools likely built by a nation-state, and they say they reverse engineered a sample they called CryptoWaters that uses the Coruna framework and leaves actionable indicators of compromise. (iverify.io)
So the headline you want to write—“government-grade iPhone hacking tools are in criminal hands”—can be accurate only if you keep the verbs disciplined: researchers say the kit looks like nation-state-grade engineering, that it appears to have moved through surveillance and espionage contexts, and that it is now used by criminals for financial theft. The origin is suggested, not proven, and the proliferation is the confirmed part. (TechCrunch)
The timeline, because the order explains the risk
February 2025, fragments in a surveillance customer operation
Google says it captured parts of an iOS exploit chain used by a “customer of a surveillance company” and that the chain was integrated into a previously unseen JavaScript framework. That tells you Coruna started life as more than a pile of PoCs; it was already an integrated delivery system. (Nube de Google)
Mid 2025, watering hole deployment against Ukrainian users
Google then observed Coruna deployed in watering hole attacks targeting Ukrainian users by UNC6353, which they assess as a suspected Russian espionage group. This stage matters operationally: the delivery model is “you browse, you lose,” which is exactly the kind of distribution that scales. (Nube de Google)
Late 2025, broad-scale financial campaigns
Google says it later retrieved the complete exploit kit when it was used in broad-scale campaigns by UNC6691, a financially motivated threat actor operating from China. Wired describes this as the moment the kit’s path becomes truly disturbing: from spies to cybercrime, with a plausible broker-mediated handoff in between. (Nube de Google)
March 3, 2026, coordinated disclosure and the “EternalBlue moment” framing
Multiple outlets quote iVerify’s “EternalBlue moment” comparison, drawing a line from the 2017 leak of an NSA-developed Windows exploit to the possibility that a comparable leak dynamic is now happening in mobile exploitation. The analogy is not perfect, but the warning is clear: once top-tier offensive tooling enters uncontrolled circulation, the downstream damage is driven by adoption, not by the original author’s intent. (TechCrunch)
How Coruna compromises an iPhone, the high level chain logic
To understand why Coruna feels like “it just works,” you need to see what the kit is actually chaining.
- Initial code execution in the browser context via WebKit web content processing flaws.
- Privilege lift and containment breakouts that escape WebContent sandboxing and reach more privileged execution contexts.
- Kernel-level control primitives through local privilege escalation and mitigation bypasses, including PPL bypass components.
- Stager and implant loading inside system daemons to establish communication and run targeted theft modules.
That pattern is not new in iOS exploitation, but Coruna’s value is that it packages multiple versions of each step so it can cover a wide OS spread. Google calls out that the kit includes non-public exploitation techniques and mitigation bypasses, plus extensive documentation in native English—this is “productized exploitation,” not opportunistic hacking. (Nube de Google)
Two defensive details in Google’s write-up are particularly operationally useful:
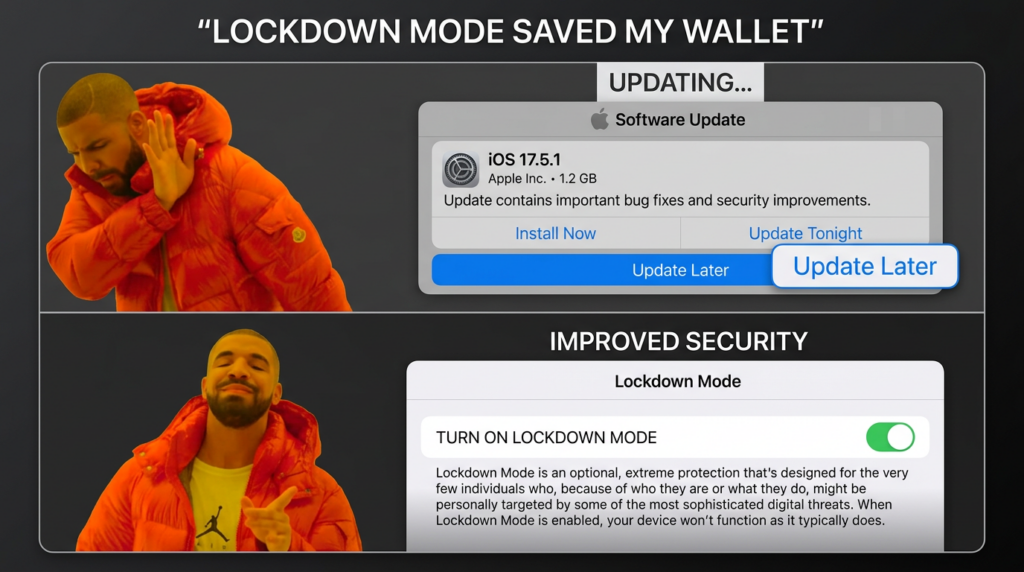
- Coruna bails out if it detects the device is in Modo Bloqueo or the user is in Private Browsing.
- It uses a hard-coded cookie to generate resource URLs, with resources referred to by a hash derived from
sha256(COOKIE + ID)[:40].
That “bail out” behavior is a rare gift to defenders because it gives you a concrete mitigation lever that doesn’t depend on Apple patch timelines, and it explains why some users may have been “missed” even on vulnerable builds. (Nube de Google)
What people keep calling this incident, and why those words matter technically
You’ll see the same phrases across the best reporting and the primary research. They are not just narrative labels; each maps to a real control point.
| Phrase you’ll see everywhere | What it really means for defenders | Where it’s grounded |
|---|---|---|
| “Exploit kit” | Not one bug: reusable framework + multiple chains + delivery + staging | Google describes five chains and 23 exploits (Nube de Google) |
| “Watering hole” | Legit sites compromised to silently attack visitors | Google and iVerify both describe waterhole deployment (Nube de Google) |
| “First known mass iOS attack” | Criminal-scale exploitation, not limited to a handful of VIP targets | iVerify press release framing (iverify.io) |
| “EternalBlue moment” | High-end tooling leaking into wider abuse ecosystem | Wired, CyberScoop, TechCrunch (WIRED) |
| “Lockdown Mode” | Attack surface reduction that Coruna explicitly checks for | Google kit behavior, Apple guidance (Nube de Google) |
| “Operation Triangulation” | Prior iOS campaign with overlap in techniques/components | Google connects Photon and Gallium, Kaspersky reports Triangulation (Nube de Google) |
If you only remember one sentence from this table, make it this: the same terms that drive headlines are also the best pivots for building a response checklist. You can turn them into requirements: “Are we exposed to watering hole delivery,” “Do we have a Lockdown Mode policy for high-risk staff,” and “Can we inspect iOS backups for known IOC footprints.”
The CVEs, the exploit components, and the patch floors that actually matter
Coruna spans years of iOS vulnerability history. The point is not that Apple failed to patch; the point is that attackers can keep old chains alive as long as real-world devices stay unpatched.
Google published a mapping table of exploit “code names,” their type, targeted versions, and the fixed versions where known. Some entries have no CVE association, and Google notes the associations may be revised as analysis continues. (Nube de Google)
Below is a defender-oriented condensation of the most decision-relevant CVEs that appear in Google’s mapping and that have solid vendor records in Apple/NVD. The goal is not to reverse engineer exploits; it’s to know which patch floors remove entire classes of exploitation.
WebKit remote code execution class, the browser foothold
CVE-2024-23222
Apple and NVD describe it as a WebKit issue where processing maliciously crafted web content may lead to arbitrary code execution, fixed in iOS 17.3 and related releases, with Apple aware it may have been exploited. (Soporte técnico de Apple)
CVE-2022-48503
Apple’s security content for iOS 15.6 states processing web content may lead to arbitrary code execution, and CISA later added this CVE to the Known Exploited Vulnerabilities catalog in October 2025. (Soporte técnico de Apple)
CVE-2023-43000
NVD and Apple document it as a WebKit use-after-free leading to memory corruption, fixed in iOS 16.6 and Safari 16.6, with Apple’s entry added later. (NVD)
Sandbox escape and kernel leverage, turning browser code exec into device control
CVE-2023-32409
NVD states a remote attacker may be able to break out of the Web Content sandbox and notes Apple was aware of active exploitation; it’s fixed in iOS 16.5 and iOS 15.7.8 among others. (NVD)
CVE-2024-23225 and CVE-2024-23296
Both are tied to bypassing kernel memory protections once an attacker already has powerful primitives; Apple/NVD note exploitation awareness language for these families and list fixed versions (iOS 17.4 for these kernel-protection bypass items in the public records). (NVD)
Why these categories chain so well on iOS
iOS has strong defense-in-depth: sandboxing (especially for WebContent), pointer authentication codes, kernel hardening, and layered memory protections. Coruna’s design is to assemble a “least fragile” path through that maze for each OS generation: if one WebKit bug stops working, another might; if one kernel bypass is patched, an older chain might still hit older phones; and if a target has a newer A-series chip, the kit chooses a chain that matches that environment. Google explicitly says Coruna includes a binary loader that chooses appropriate chains post-RCE and that payload blobs carry metadata about supported chips and versions. (Nube de Google)
That’s why patch floors matter more than CVE obsession. Your practical question is: what’s the oldest iOS build in your fleety does the attacker still have a chain that covers it?
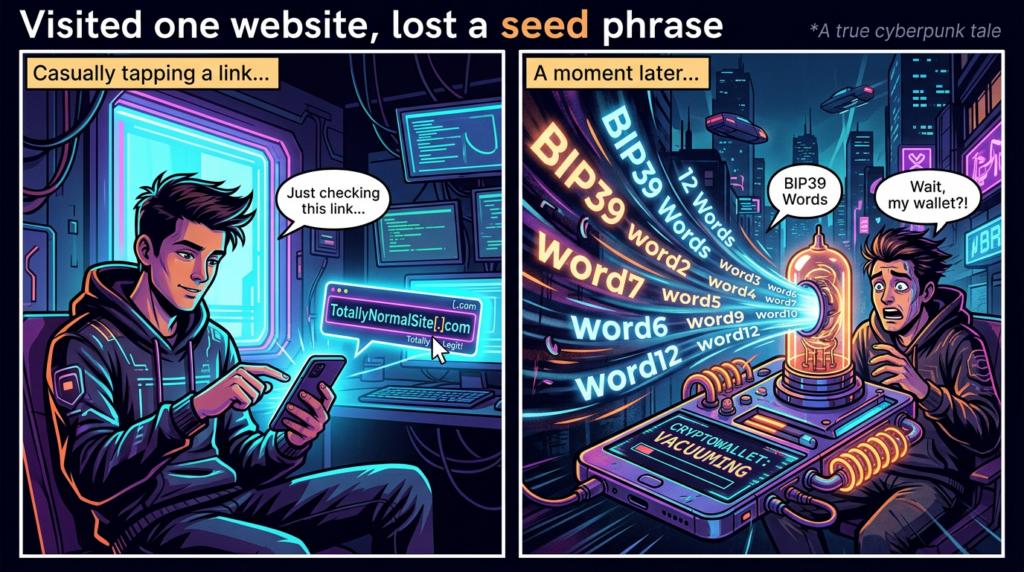
The payload, why this looks like theft tooling not classic spyware
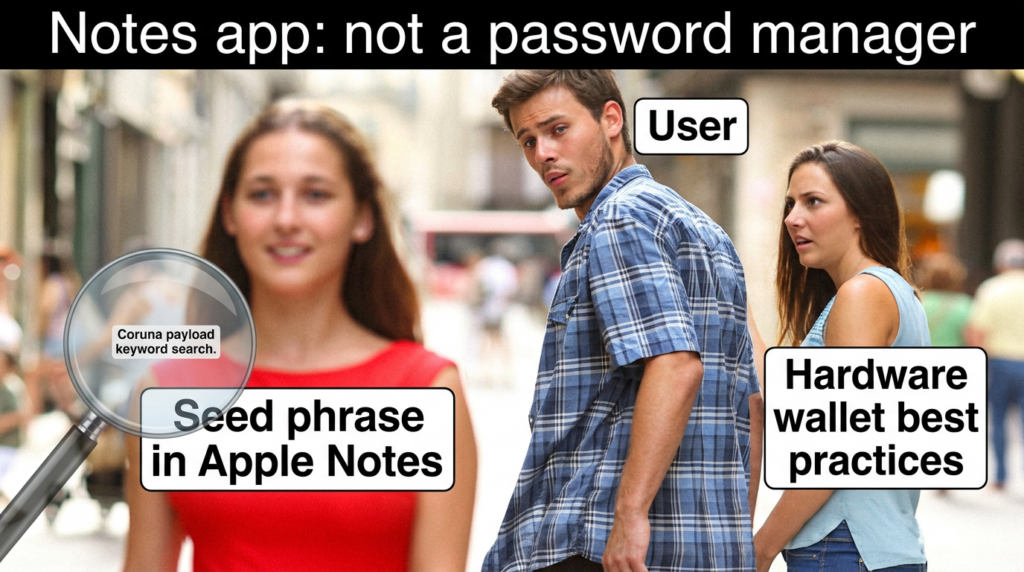
Google’s most important technical observation about Coruna is at the end of the chain. The stager binary PlasmaLoader, tracked as PLASMAGRID, injects itself into powerd running as root, and the resulting payload is oriented toward stealing financial information rather than the “usual capabilities” expected from a surveillance vendor. (Nube de Google)
Google describes several theft behaviors that are unusually concrete for public reporting:
- decoding QR codes from images on disk
- analyzing text blobs for BIP39 word sequences
- searching for keywords like “backup phrase” or “bank account”
- exfiltrating relevant text if found in Apple Notes
This is the precise bridge from “device compromise” to “money loss.” A compromised iPhone is not automatically a cash machine, but if a victim stores seed phrases in Notes or screenshots, or uses multiple mobile wallet apps, the attacker can turn a one-time browser exploit into recurring theft value. (Nube de Google)
Google also lists a set of targeted wallet apps via bundle identifiers, including MetaMask and several others, which strongly supports the “crypto theft modules” framing. (Nube de Google)
iVerify’s deeper technical write-up describes a multi-stage implant flow across processes, including fetching configuration from one domain and then using another for command-and-control, with later modules being loaded depending on installed apps. (iverify.io)
The implication for responders is uncomfortable but actionable: if you are investigating a suspected Coruna-style infection, you must treat wallet seed handling as part of incident response. The remediation is not just “update iOS.” It’s also “assume any seed phrase or private key stored on-device may be compromised” and act accordingly.
Is this really “a leaked US government framework” and how to talk about it without overclaiming
This is the part that gets clicks—and also the part that falls apart fastest if you get sloppy.
What iVerify says in its press release is that GTIG refers to UNC6691 using a sophisticated exploit chain developed by a spyware vendor, and that iVerify assesses the framework has similarities to previous frameworks developed by threat actors affiliated with the US government. They also say the same framework was observed by Russian threat actors targeting Ukrainians. (iverify.io)
TechCrunch summarizes that iVerify linked the Coruna exploit kit to the U.S. government based on similarities to previously attributed tools, while also emphasizing the broader point: regardless of origin, these tools will end up “in the wild.” (TechCrunch)
Wired is careful but pointed: it highlights clues like English-language coding and overlap with components seen in Operation Triangulation, while still calling the origin “possible” and noting the US government didn’t respond to attribution claims. (WIRED)
CyberScoop and Nextgov reinforce the same framing: plausible linkage, not certainty, and the core risk is the proliferation market for “second hand” zero-days. (CyberScoop)
If you want a defensible headline and you want it to survive criticism, write it this way:
Confirmed: a nation-state-grade iPhone exploit kit proliferated across actors and is now used in criminal campaigns. (Nube de Google)
Plausible but not proven: parts of the framework resemble tools previously attributed to US-affiliated operators. (iverify.io)
Unknown: exactly how the tool moved hands. (Nube de Google)
That is enough to justify urgency without turning your article into speculation.
Who is actually vulnerable, and why “old iOS” is the real attack surface
Google’s coverage range is explicit: iOS 13.0 through iOS 17.2.1, which spans devices and releases from 2019 through late 2023. (Nube de Google)
They also state Coruna is not effective against the latest iOS and urge users to update; if an update is not possible, enable Lockdown Mode. (Nube de Google)
Wired adds an important nuance: Google noted the kit targets vulnerabilities in WebKit for browsers, so Safari users on those older versions are vulnerable, and Coruna checks for Lockdown Mode and won’t attempt exploitation if it’s enabled. (WIRED)
This leads to the most useful risk segmentation you can give readers:
- Out-of-date iPhones are the target class. If you still have iOS 15.x or 16.x on a phone that could update, you’re choosing to stay inside the blast radius.
- People who can’t update are structurally exposed. Older devices that cannot run newer iOS versions are exactly what “long-lived exploit kits” are built to harvest.
- Crypto users are a multiplier. Not because crypto is special, but because many users store high-value secrets locally, and Coruna’s payload is tuned to find them. (Nube de Google)
- Travel and geopolitical exposure increases the odds. Watering hole delivery often clusters around specific populations and web destinations. (Nube de Google)
- Enterprises without mobile telemetry will miss this. iOS is hard to inspect “from the inside,” which is exactly why forensic approaches rely on backups, sysdiagnose, and specialized tooling. (Securelist)
What to do right now, a prioritized checklist that maps to the actual mechanics
1 Update iOS, because Coruna’s compatibility window is the whole problem
This is the least glamorous recommendation and the most effective one. Google’s own conclusion is that Coruna is not effective against the latest iOS, and the kit’s known coverage stops at iOS 17.2.1. (Nube de Google)
2 Turn on Lockdown Mode for high risk users and roles
Lockdown Mode is not just “extra security.” It’s a mode that Coruna explicitly checks for and avoids, and Apple describes it as an extreme optional protection for rare, sophisticated attacks. (Nube de Google)
Apple’s official step path is straightforward: Settings → Privacy & Security → Lockdown Mode → Turn On Lockdown Mode. (Soporte técnico de Apple)
3 Use Private Browsing as a stopgap when you cannot enable Lockdown Mode
Google states Coruna bails out if the user is in private browsing. This is not a perfect defense and it is not a substitute for patching, but it can reduce exposure in constrained scenarios. (Nube de Google)
4 Assume secrets stored on-device are compromised if you have any infection signal
Because the payload is tuned to find BIP39 sequences and wallet app modules, if you have any credible indicator of infection you should treat seed phrases, screenshots of QR codes, Notes entries, and potentially wallet session tokens as burned. (Nube de Google)
5 Treat this as a web security issue too, not only a device security issue
Coruna’s delivery model includes malicious web content and watering hole style attacks. That means your organization’s websites and third-party analytics dependencies can become the attack surface that compromises your own users. (Nube de Google)
Detection, what you can actually verify without magical iOS root access
iVerify’s IOC driven approach and public checking
iVerify says it reverse engineered CryptoWaters, built IOCs, and deployed them in its Enterprise product and also into its Basic app made free for a limited period to help the public check for infection. (iverify.io)
Sysdiagnose and process behavior indicators
iVerify publishes process-based IOCs like thread names and dispatch queues (for example strings starting with plasma_ inside processes like powerd y locationd) and indicates where they show up in sysdiagnose artifacts like stacks.ips. (iverify.io)
Backup forensics, why MVT remains relevant
Kaspersky’s Operation Triangulation write-up explains a foundational constraint: it is “impossible to inspect modern iOS devices from the inside,” so investigators create offline backups and inspect them using Mobile Verification Toolkit. That same reality applies here: backups and derived timelines are the pragmatic place to hunt. (Securelist)
Even if you do not use MVT end-to-end, you can still query the key SQLite databases in a backup for the signals iVerify lists: Safari history artifacts, WebKit storage databases, and any recorded infection domain URLs. (iverify.io)
A practical IOC table you can hand to an incident responder
Below is a condensed version of the most actionable IOC categories described by iVerify and Google, framed as “what you can check” and “where.”
| IOC category | Example signal | Where to look | Por qué es importante |
|---|---|---|---|
| Process and thread names | plasma_* thread names | sysdiagnose stacks and crash artifacts | Strong hint of implant execution inside system daemons (iverify.io) |
| File artifacts | /private/var/tmp/pl.core.lock and related temp files | filesystem traces, backup artifacts when present | Implant staging and runtime markers (iverify.io) |
| Network domains | .xyz C2 domains and named infra | network logs, DNS, secure web gateways | Coruna uses explicit C2 lists and DGA fallback patterns (Nube de Google) |
| Exploit infrastructure | exploit server domains in iVerify blog | Safari history and WebKit DBs in backups | Evidence of exposure to delivery URLs (iverify.io) |
| Behavioral checks | bails out on Lockdown Mode / Private Browsing | device config, browsing mode | A mitigation you can enforce and verify (Nube de Google) |
Code and queries, safe defensive examples you can publish without enabling abuse
1 SQL, quickly check an iPhone backup Safari history for suspicious domains
You’ll need to locate History.db in the extracted iPhone backup. Paths vary by backup format and extraction method, but the query shape is stable.
-- Safari History.db
-- Look for known suspicious host fragments or high-entropy .xyz domains
SELECT
datetime(history_visits.visit_time + 978307200, 'unixepoch') AS visit_datetime_utc,
history_items.url,
history_items.domain_expansion
FROM history_items
JOIN history_visits ON history_items.id = history_visits.history_item
WHERE
history_items.url LIKE '%.xyz/%'
OR history_items.url LIKE '%/group.html%'
OR history_items.url LIKE '%/details/%'
ORDER BY history_visits.visit_time DESC
LIMIT 200;
This does not “prove compromise,” but it can rapidly prove exposure to delivery infrastructure when paired with iVerify’s observed domains list. (iverify.io)
2 Python, scan an extracted iTunes style backup for IOC strings and domains
This is deliberately conservative: it looks for obvious IOC strings in plaintext files and for suspicious domain patterns in extracted databases or logs you can export to text.
import os
import re
from pathlib import Path
IOC_STRINGS = [
# iVerify / Google themes
"com.plasma.", "plasma_", "PLASMAGRID", "PlasmaLoader",
# Common Coruna URL patterns called out in reports
"/group.html", "/details/show.html", "/details/new.js",
]
DOMAIN_PAT = re.compile(r"\\b[a-z0-9]{10,20}\\.xyz\\b", re.IGNORECASE)
def scan_path(root: Path, max_bytes: int = 8_000_000):
hits = []
for p in root.rglob("*"):
if not p.is_file():
continue
try:
if p.stat().st_size > max_bytes:
continue
data = p.read_bytes()
except Exception:
continue
# Cheap binary to text view
try:
text = data.decode("utf-8", errors="ignore")
except Exception:
continue
for s in IOC_STRINGS:
if s in text:
hits.append((str(p), f"string:{s}"))
for m in DOMAIN_PAT.findall(text):
hits.append((str(p), f"domain:{m.lower()}"))
return hits
if __name__ == "__main__":
root = Path(os.environ.get("BACKUP_DIR", ".")).resolve()
results = scan_path(root)
for path, hit in results[:500]:
print(f"{hit}\\t{path}")
print(f"\\nTotal hits: {len(results)}")
Pair this with a controlled, curated domain list from Google’s published C2 list if you want high confidence matching. (Nube de Google)
3 Network detection idea, why .xyz is not enough and what to log instead
Google notes Coruna’s implant uses a hard-coded C2 list and a fallback mechanism that includes a domain generation algorithm seeded with the string “lazarus,” generating predictable 15-character .xyz domains and checking activity via Google’s public DNS resolver. (Nube de Google)
That means “block .xyz” is not the lesson. The lesson is: log and alert on unexpected system processes making outbound HTTPs requests, and on DNS patterns that match high-entropy short labels clustered in time.
If you have enterprise DNS logs, you can build detections like:
- device resolves multiple 15-char
.xyzdomains within minutes - same device then makes outbound HTTPS POSTs to one of them
- user agent anomalies like system processes (
powerd,imagent) presenting nonstandard UA strings, which iVerify notes as suspicious (iverify.io)
A disciplined incident response playbook for Coruna style compromise
Step 1 Confirm exposure vs compromise
Exposure means the device visited or loaded the delivery URL. Compromise means you see process IOCs, file artifacts, or network C2 communication patterns.
Because iOS is hard to introspect, you’ll often proceed with “credible suspicion” rather than courtroom-grade certainty. That is normal in mobile IR. (Securelist)
Step 2 Contain the money path first
If the user has mobile wallets:
- move funds to new wallets using a clean device
- rotate keys and revoke sessions where possible
- treat any seed phrase that lived in Notes, screenshots, or files on the phone as compromised, because the payload explicitly hunts for BIP39 patterns and “backup phrase” keywords (Nube de Google)
Step 3 Contain the account path
Even if the campaign focus is crypto theft, a compromised phone can become an identity pivot. Reset Apple ID credentials, ensure 2FA is intact, and review device trust lists. This is standard hygiene, and it limits secondary fallout.
Step 4 Preserve artifacts before you wipe
Collect sysdiagnose and an encrypted backup if policy allows. Once you wipe and restore, you will lose much of the evidence needed to understand scope and entry point. (iverify.io)
Step 5 Eradicate and verify
Update iOS to a non-vulnerable version, re-enable Lockdown Mode for the right users, and then verify via policy compliance that devices stay above patch floors.
Coruna’s most scalable delivery pattern is web-based: malicious websites, watering holes, and injected components that “just happen” to get served to visitors. That means the defender’s job is not only device patching; it’s also ensuring your own web properties cannot be repurposed into someone else’s exploit distribution layer. Google explicitly describes Coruna’s delivery through malicious web content and watering hole style operations, and iVerify’s analysis starts from discovering a suspicious domain hosting exploits. (Nube de Google)
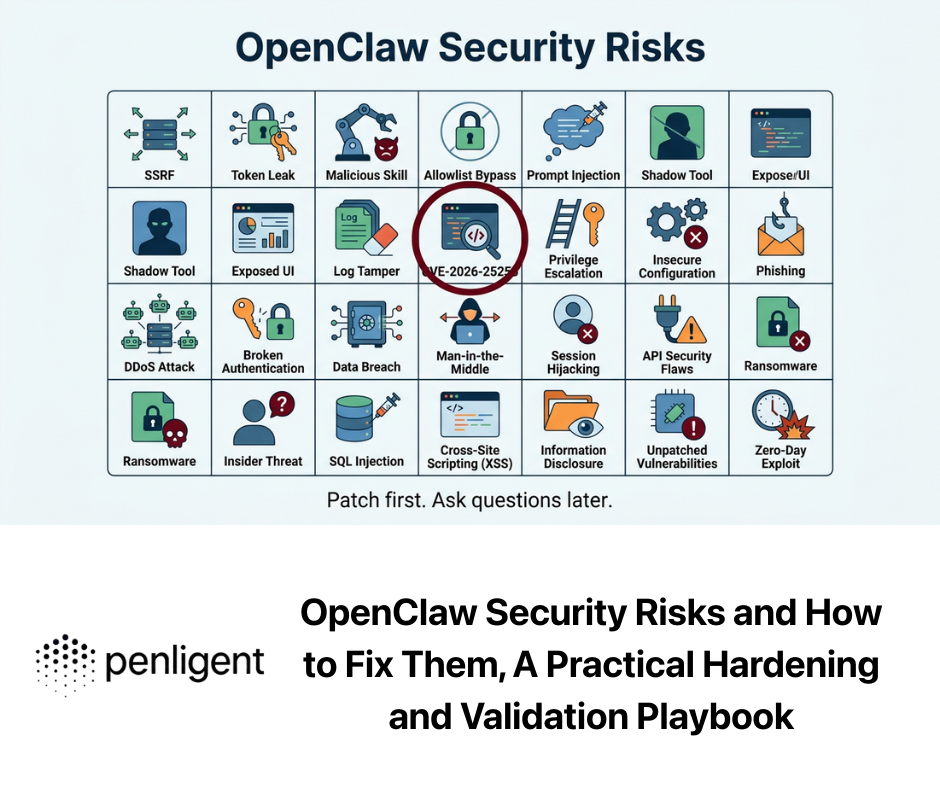
This is where an AI-driven pentest platform can contribute without pretending to “scan iPhones.” With Penligent, teams can continuously test their public web assets for the classes of failures that enable watering holes: outdated CMS plugins, script injection points, insecure third-party analytics loading, and hidden redirects that route users to attacker-controlled infrastructure. When incidents like Coruna break, speed matters: you want fast asset discovery, fast reproduction in a safe lab, and a report that maps exactly what to fix and how to verify the fix is real. (Penligente)
A second natural fit is evidence-driven verification. When the world learns that “just visiting a site can compromise an iPhone,” executives ask whether your organization’s pages could be used the same way. Penligent is designed around turning natural-language security questions into precise, tool-backed checks across a real environment, so teams can answer quickly: “Are any of our pages serving unexpected scripts,” “Do we have third-party includes that changed recently,” “Can we prove integrity of the content pipeline,” and “Which domains do our pages call out to at runtime.” (Penligente)
The bigger lesson, exploit markets do not respect your threat model
Google frames Coruna as another example of sophisticated capabilities proliferating and points to an active market for “second hand” zero-day exploits. iVerify emphasizes that once spyware capabilities are sold, control over end customers is lost and the market is highly unregulated. (Nube de Google)
The uncomfortable reality is that modern mobile exploitation is now following the same arc we watched on desktop a decade ago: a small set of elite actors fund development, brokers move capabilities, and criminals industrialize the last mile. The result is not that every iPhone is doomed; the result is that patch lag becomes a monetizable asset.
If you want a single sentence to end the article on, make it this: Coruna is what happens when “old iOS” becomes an economic opportunity. (Nube de Google)
Further reading
Google Threat Intelligence Group, Coruna: The Mysterious Journey of a Powerful iOS Exploit Kit https://cloud.google.com/blog/topics/threat-intelligence/coruna-powerful-ios-exploit-kit
iVerify press release, iVerify Details First Known Mass iOS Attack https://iverify.io/press-releases/first-known-mass-ios-attack
iVerify technical blog, Coruna: Inside the Nation-State-Grade iOS Exploit Kit We’ve Been Tracking https://iverify.io/blog/coruna-inside-the-nation-state-grade-ios-exploit-kit-we-ve-been-tracking
TechCrunch coverage, A suite of government hacking tools targeting iPhones is now being used by cybercriminals https://techcrunch.com/2026/03/03/a-suite-of-government-hacking-tools-targeting-iphones-is-now-being-used-by-cybercriminals/
WIRED coverage, A Possible US Government iPhone-Hacking Toolkit Is Now in the Hands of Foreign Spies and Criminals https://www.wired.com/story/coruna-iphone-hacking-toolkit-us-government/
Apple Support, About Lockdown Mode https://support.apple.com/en-us/105120
Apple User Guide, Turn on Lockdown Mode on iPhone https://support.apple.com/guide/iphone/use-lockdown-mode-iph845f6f40c/ios
Apple security content, iOS 17.3 and iPadOS 17.3, includes CVE-2024-23222 https://support.apple.com/en-us/120304
Apple security content, iOS 17.4 and iPadOS 17.4, includes CVE-2024-23225 and other items https://support.apple.com/en-us/120893
Apple security content, iOS 15.6 and iPadOS 15.6, includes CVE-2022-48503 https://support.apple.com/en-us/102892
NVD, CVE-2024-23222 https://nvd.nist.gov/vuln/detail/CVE-2024-23222
NVD, CVE-2022-48503, includes CISA KEV metadata https://nvd.nist.gov/vuln/detail/CVE-2022-48503
CISA alert, CVE-2022-48503 added to KEV Catalog https://www.cisa.gov/news-events/alerts/2025/10/20/cisa-adds-five-known-exploited-vulnerabilities-catalog
Kaspersky Securelist, Operation Triangulation https://securelist.com/operation-triangulation/109842/
Penligent related articles
CVE-2025-24085 iOS 0-Day Explained: Public PoC and the Role of AI Pentest Tools https://www.penligent.ai/hackinglabs/cve-2025-24085-an-ios-0-day-public-poc-and-the-role-of-ai-pentest-tools/
Safari passwords, Deep Technical Guide for Security Engineers https://www.penligent.ai/hackinglabs/safari-passwords-deep-technical-guide-for-security-engineers/
OpenClaw + VirusTotal: The Skill Marketplace Just Became a Supply-Chain Boundary https://www.penligent.ai/hackinglabs/openclaw-virustotal-the-skill-marketplace-just-became-a-supply-chain-boundary/
Penligent overview, Natural-Language Orchestration for AI Automated Penetration Testing https://www.penligent.ai/hackinglabs/penligent-ai-natural-language-orchestration-for-ai-automated-penetration-testing/