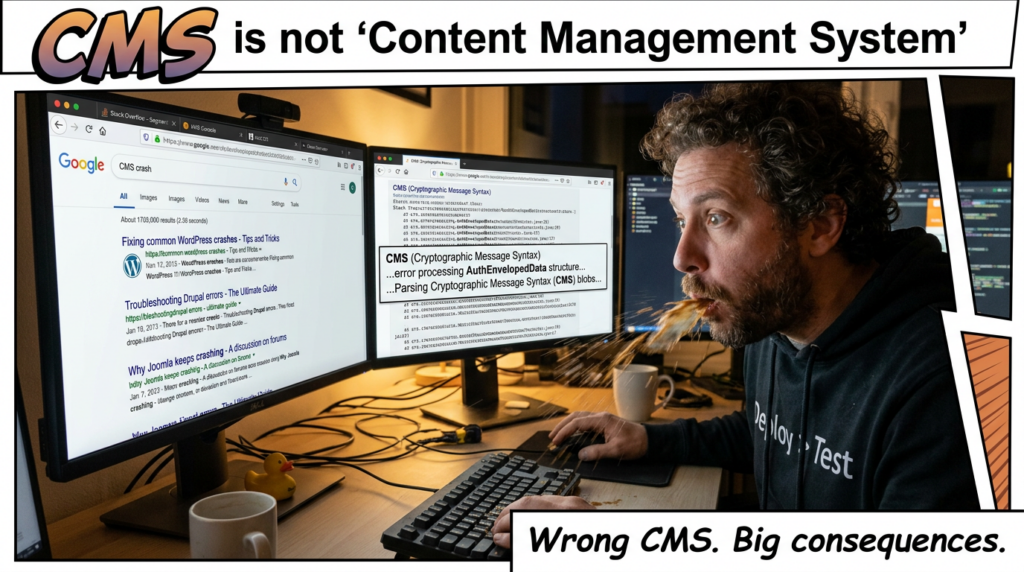
Most vulnerability posts about OpenSSL follow the same script: “critical library,” “used everywhere,” “patch now.” That framing gets attention, but it does not help an engineer decide what to do next. CVE-2025-15467 deserves a more careful read. It is a real and serious bug in OpenSSL’s CMS parsing logic, specifically in the handling of AuthEnvelopedData and EnvelopedData structures that use AEAD ciphers such as AES-GCM. The flaw allows an attacker to supply a crafted CMS message with an oversized IV and trigger a stack-based out-of-bounds write before authentication or tag verification occurs. OpenSSL published it on January 27, 2026 as a High-severity issue, and CISA’s ADP entry scored it 9.8 with a network, no-privileges, no-user-interaction vector. (openssl-library.org)
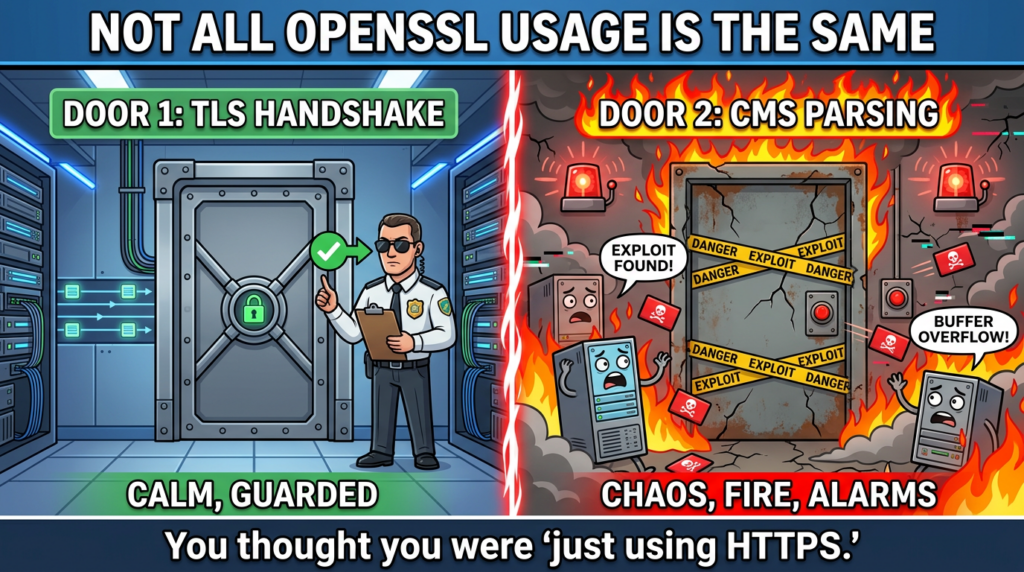
That combination explains why the bug attracted immediate attention. A pre-auth stack write in a cryptographic library is not background noise. But the part many posts miss is equally important: this is not a blanket “every TLS server is remotely exploitable” event. Whether CVE-2025-15467 is reachable depends on whether your application actually parses untrusted CMS or PKCS#7 content through the vulnerable OpenSSL path. In practice, that means the highest-risk environments are things like S/MIME-capable mail clients, secure email gateways, certificate processing or import pipelines, PKI and CA tooling, and any product that accepts uploaded or inbound CMS objects from outside trust boundaries. Datadog’s analysis makes this distinction clearly, and Node.js’ own security assessment explicitly states that CVE-2025-15467 does not affect Node.js on any branch because Node.js does not use the CMS APIs involved. (Datadog Security Labs)
That is the right mental model for this vulnerability. CVE-2025-15467 is not “OpenSSL is broken everywhere.” It is “a dangerous OpenSSL parsing path becomes high priority when your product ingests untrusted CMS structures.” If you operate software that never touches CMS AuthEnvelopedData, this is unlikely to be your biggest OpenSSL problem this quarter. If you run infrastructure that decrypts or inspects S/MIME messages, accepts PKCS#7 content, or wraps OpenSSL CMS APIs in business logic exposed to external users, then CVE-2025-15467 moves from advisory to incident-response material very quickly. (Datadog Security Labs)
What CVE-2025-15467 actually is
The authoritative description is unusually direct. NVD states that when OpenSSL parses CMS (Auth)EnvelopedData structures using AEAD ciphers such as AES-GCM, the IV encoded in ASN.1 parameters is copied into a fixed-size stack buffer without verifying that its length fits the destination. An attacker can provide a crafted CMS message with an oversized IV, causing a stack-based out-of-bounds write before authentication or tag verification occurs. NVD also notes that because the overflow happens before authentication, no valid key material is required to trigger it. (NVD)
OpenSSL’s own vulnerability page says the issue is titled “Stack buffer overflow in CMS (Auth)EnvelopedData parsing,” was published on January 27, 2026, and affects OpenSSL 3.0.0 before 3.0.19, 3.3.0 before 3.3.6, 3.4.0 before 3.4.4, 3.5.0 before 3.5.5, and 3.6.0 before 3.6.1. The OpenSSL security advisory further states that the FIPS modules are not affected because the CMS implementation is outside the FIPS module boundary, and that OpenSSL 1.1.1 and 1.0.2 are not affected. (openssl-library.org)
NVD’s CISA-ADP metrics assign a CVSS 3.1 score of 9.8 with vector AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H. That score should not be read as proof that stable, internet-scale RCE is trivial in every environment. It should be read as a signal that the vulnerability is remote, unauthenticated, severe in outcome, and dangerous enough that defenders should not wait for exploit kits to settle the debate. Even NVD’s description frames the result carefully: the flaw may lead to denial of service or potentially remote code execution. That wording matters. It is high-confidence DoS with plausible RCE conditions, not guaranteed one-shot RCE everywhere. (NVD)
The search intent around CVE-2025-15467 is already clear
A useful way to write about a vulnerability is to look at what the current search landscape is actually rewarding. Based on the current SERP titles and summaries from OpenSSL, NVD, Datadog, JFrog, Orca, SentinelOne, CyCognito, and others, the most persistent keyword cluster around this CVE is not just the literal ID. The dominant companion phrases are “OpenSSL,” “RCE,” “pre-auth,” “CMS,” “AuthEnvelopedData,” “stack buffer overflow,” “AES-GCM,” and “affected versions.” In other words, the market is not looking for a generic definition page. It is looking for an answer to four operational questions: what is the bug, where is it reachable, is RCE real, and what exact versions need patching. (Orca Security)
That also explains why headlines across security vendors converge on very similar framing. Orca emphasizes “Critical OpenSSL Flaw Enables Pre-Auth Remote Code Execution.” JFrog uses “Potentially Critical RCE Vulnerability in OpenSSL.” Datadog chooses a more measured formulation but still highlights pre-auth stack overflow and the possibility of code execution. Those titles should not be treated as objective click-through-rate telemetry, because they are not. But they are a strong real-time indicator of what publishers believe users want when they search this CVE right now. The best query expansions to cover in a serious article are therefore things like “CVE-2025-15467 OpenSSL,” “CVE-2025-15467 RCE,” “CVE-2025-15467 CMS buffer overflow,” and “CVE-2025-15467 pre-auth.” (Orca Security)
If you are structuring internal documentation, advisories, product notes, or vulnerability verification playbooks, those are the phrases worth mapping. “OpenSSL bug” is too broad. “CVE-2025-15467 pre-auth CMS stack overflow” is much closer to what both humans and retrieval systems will recognize as the real topic. (Orca Security)
Root cause, why an oversized IV becomes a stack write
Datadog’s write-up is one of the clearest public technical explanations. It highlights the function evp_cipher_get_asn1_aead_params(), where OpenSSL reads the ASN.1 octet string length, then uses the returned length in a second call that copies data into a fixed-size local buffer iv[EVP_MAX_IV_LENGTH]. The key problem is that the helper returns the full length even when it exceeds EVP_MAX_IV_LENGTH, so the second copy can exceed the size of the stack buffer. That means the attacker controls both the length and the content being written into stack memory. Because it happens before authentication, the parser crashes before any cryptographic legitimacy is established. (Datadog Security Labs)
JFrog’s analysis aligns with that explanation and makes the exploitability consequence plain: OpenSSL did not verify whether the IV size exceeded the fixed-size stack buffer before copying it. JFrog also says its researchers reproduced the issue and observed vulnerable cases in applications that invoke OpenSSL CMS-related APIs such as CMS_decrypt, PKCS7_decrypt, CMS_EnvelopedData_decrypt, ו EVP_CIPHER_asn1_to_param, as well as command-line tooling paths like openssl cms ו openssl smime. (JFrog Security Research)
That technical shape matters because it separates this bug from vague “memory corruption” language that tells defenders very little. This is not a diffuse heap condition that might depend on obscure allocator state. It is a stack-based write primitive at message-parse time, before authentication, on attacker-controlled input. That is exactly the sort of primitive that becomes operationally dangerous when exposed through a service boundary. (Datadog Security Labs)
Why the “pre-auth” detail is not just headline bait
“Pre-auth” gets overused in vulnerability marketing, but here it is the right term. OpenSSL and NVD both describe the overflow as happening before authentication or tag verification. That means the attacker does not need a valid key, a trusted certificate, or any legitimate AEAD-authenticated content. They only need to deliver a parser-reachable CMS object whose IV length is malicious. (NVD)
That said, pre-auth does not automatically mean remotely reachable over the public internet in your environment. The actual question is whether your application exposes a pre-auth parser boundary for CMS input. A web app that links against OpenSSL but only uses it for normal TLS handshakes is not in the same risk category as an email gateway that decrypts inbound S/MIME payloads from arbitrary senders. Datadog explicitly notes this distinction and says that if you only use OpenSSL for TLS handshakes and never accept CMS or PKCS#12 from untrusted sources, these issues are unlikely to be reachable. (Datadog Security Labs)
For a security team, that is the operational pivot. The triage question is not “Do we have OpenSSL somewhere?” The triage question is “Do we have a reachable parser path for untrusted CMS AuthEnvelopedData or related PKCS#7 content?” That is a much narrower and much more useful question. (Datadog Security Labs)
Affected versions, unaffected versions, and patch targets
OpenSSL’s own vulnerability page is the clearest source for version scope. CVE-2025-15467 affects the following version ranges:
| סניף | Vulnerable range | Fixed version |
|---|---|---|
| OpenSSL 3.6 | 3.6.0 before 3.6.1 | 3.6.1 |
| OpenSSL 3.5 | 3.5.0 before 3.5.5 | 3.5.5 |
| OpenSSL 3.4 | 3.4.0 before 3.4.4 | 3.4.4 |
| OpenSSL 3.3 | 3.3.0 before 3.3.6 | 3.3.6 |
| OpenSSL 3.0 | 3.0.0 before 3.0.19 | 3.0.19 |
OpenSSL 1.1.1 and 1.0.2 are not affected, and the FIPS modules in the 3.x line are not affected because the CMS implementation sits outside the FIPS module boundary. (openssl-library.org)
That distinction matters because many patch advisories in downstream products will simplify the story to “OpenSSL issue, update now,” which is directionally right but incomplete. If you are inventorying risk across a large estate, you want branch-accurate logic. A scanner rule that flags all OpenSSL versions without regard to whether they are 1.1.1, 1.0.2, or 3.x will create a lot of unnecessary noise for this particular CVE. (openssl-library.org)
Node.js is a good example of why branch- and feature-aware interpretation matters. Node’s official assessment says CVE-2025-15467 does not affect Node.js on any branch because Node.js does not use the CMS APIs involved. In the same post, Node explains that other OpenSSL issues from the January 2026 advisory do matter for Node because they flow through PFX handling, but CVE-2025-15467 specifically does not. That is a reminder that “bundles vulnerable OpenSSL” and “exposes vulnerable path” are not identical statements. (Node.js)
The real attack surface, where defenders should actually look
The most important sentence in Datadog’s analysis may be the simplest one: the relevant environments are those that parse untrusted CMS AuthEnvelopedData, commonly used in S/MIME and PKCS#7 workflows, or verify MACs on untrusted PKCS#12 files in certificate import paths. It also points to likely tooling categories such as S/MIME email clients, email security gateways, certificate import/export services, PKI/CA tooling, and applications that accept uploaded CMS or PKCS#12 files. (Datadog Security Labs)
That immediately gives you a practical prioritization map.
If you run an internet-facing secure email gateway that decrypts inbound S/MIME messages, you should assume this bug is worth urgent validation even if you have not seen public mass exploitation. If you maintain internal certificate-management tooling that allows users or partners to upload PKCS#7 or CMS objects, you should treat the parser boundary as suspect until proven patched. If you operate a product where OpenSSL is present but used only for standard TLS connections and never for CMS content handling, patching still matters, but the urgency calculation is different because reachability is lower. (Datadog Security Labs)
This is why vulnerability management teams often struggle with OpenSSL advisories. The instinct is to map “critical crypto library” directly to “full estate emergency.” But the better way to handle CVE-2025-15467 is to rank systems by message parsing exposure, not just package presence. Presence is step one. Reachability is what decides where incident-level work starts. (Datadog Security Labs)
Is remote code execution real, or just theoretically possible
The most defensible answer is this: potential RCE is credible, but environment-dependent. OpenSSL’s own description says the flaw may cause denial of service or potentially remote code execution. NVD preserves that wording. Datadog says code execution is possible due to the stack-based write primitive, while also noting that real-world exploitability will be hampered by platform and toolchain mitigations. JFrog goes further and states that its research team successfully achieved code execution, while also noting that real-world exploitation may require bypassing mitigations such as stack canaries, ASLR, and DEP, possibly with the aid of an information leak. (NVD)
That is about as clear as public security writing gets. You do not need to oversell this bug to justify remediation. It already justifies remediation. The safe interpretation is not “RCE is easy,” and it is not “RCE is probably fake.” The safe interpretation is “the primitive is dangerous enough that serious researchers achieved code execution in at least some conditions, while real-world reliability will vary by target.” (Datadog Security Labs)
Defenders should resist two common mistakes here. The first is downplaying the issue because exploitability is not universal. Many high-impact vulnerabilities are environment-sensitive. The second is assuming that a proof of concept against a lab build means your production stack is equally exposed. Compiler flags, memory layout, containerization, hardened builds, and whether your service actually reaches the vulnerable parser path all matter. (Datadog Security Labs)
A simple technical walkthrough of the vulnerable path
At a high level, the flow looks like this:
- An application receives CMS or PKCS#7 content from an untrusted source.
- It calls OpenSSL CMS parsing or decryption routines.
- The parser encounters AuthEnvelopedData or EnvelopedData using an AEAD cipher such as AES-GCM.
- The IV inside ASN.1 parameters is read.
- OpenSSL copies attacker-controlled IV content into a fixed-size stack buffer without adequately constraining the length.
- The process crashes, or in some environments, the stack corruption may be shaped into code execution. (NVD)
A simplified pseudo-representation of the dangerous logic looks like this:
int parse_aead_iv(ASN1_TYPE *type, params *out) {
unsigned char iv[EVP_MAX_IV_LENGTH];
int i = get_octet_string_length(type); // attacker influences length
if (i <= 0) return -1;
// danger: second copy uses i even if i > EVP_MAX_IV_LENGTH
get_octet_string_bytes(type, iv, i);
memcpy(out->iv, iv, i);
out->iv_len = i;
return i;
}
That is not the exact OpenSSL source, but it captures the bug class: an attacker-influenced length is allowed to drive a copy into fixed-size stack storage. Datadog’s published snippet and explanation show the real function and why the returned length can exceed EVP_MAX_IV_LENGTH. (Datadog Security Labs)

Reproducing the denial-of-service side, carefully
Public research has already shown that the bug can be reproduced as a crash. Datadog provides an example using the openssl cms -decrypt command against a specially crafted PEM file, producing a stack-smashing termination. JFrog says it reproduced the bug via the CMS_Decrypt API directly. That means defenders do not need to invent an attack theory from scratch; the public evidence already supports the claim that this is at least a practical parser crash when the vulnerable path is reachable. (Datadog Security Labs)
A safe validation workflow in a lab might look like this:
# confirm your local OpenSSL version
openssl version -a
# check whether cms/smime tooling is present
openssl list -commands | egrep 'cms|smime'
# in a controlled lab only, test parsing of a known benign sample first
openssl cms -inform PEM -in benign.pem -cmsout -print
# then validate patched behavior after upgrade
openssl version
# expected fixed targets:
# 3.6.1 / 3.5.5 / 3.4.4 / 3.3.6 / 3.0.19
Do not use production systems as crash-testing sandboxes, and do not assume the command-line tool is the only relevant surface. The real risk is often an application-linked library path, not a human manually invoking openssl cms. (JFrog Security Research)
Why “we only use OpenSSL for HTTPS” is sometimes true and sometimes dangerously incomplete
One of the best parts of the January 2026 coverage is that multiple sources push back against the lazy assumption that every OpenSSL CVE is mainly a TLS-handshake issue. Datadog explicitly says that if you only use OpenSSL for TLS handshakes and never accept CMS or PKCS#12 from untrusted sources, these issues are unlikely to be reachable. Node.js similarly concludes that CVE-2025-15467 does not affect Node.js because Node does not use the CMS APIs involved. (Datadog Security Labs)
But that sentence becomes dangerous when teams use it too broadly. Many environments do “only use OpenSSL for HTTPS” at the infrastructure layer but also have supporting tools, plugins, import utilities, middleware, and email or certificate workflows elsewhere in the organization that parse CMS content. In large estates, exposure often hides in adjacent systems rather than primary application servers. The right question is not “Does our web tier use CMS?” It is “Do any services in our trust boundary parse untrusted CMS or PKCS#7 objects using the vulnerable OpenSSL branches?” (Datadog Security Labs)
That is especially relevant for security teams handling M&A environments, old mail gateways, partner certificate workflows, and legacy PKI utilities. Those systems frequently survive architecture modernization because they are “working fine” until a parser bug proves otherwise. (Datadog Security Labs)
Related CVEs you should understand alongside CVE-2025-15467
The closest related issue is CVE-2025-11187, disclosed in the same January 2026 OpenSSL batch. OpenSSL describes it as improper validation of PBMAC1 parameters in PKCS#12 MAC verification. Datadog explains that in OpenSSL 3.4 and later, PBKDF2 parameters can be taken directly from the file, and attacker-controlled key length can overflow a fixed stack buffer during MAC verification. OpenSSL marked it lower than CVE-2025-15467, and Node.js’ January 2026 advisory says this one does affect multiple newer Node branches because it flows through PFX handling. (openssl-library.org)
That comparison is useful because it shows how different OpenSSL bugs have different application reachability despite living in the same disclosure set. CVE-2025-15467 is more severe in primitive and score, but Node is unaffected because it does not use the CMS APIs involved. CVE-2025-11187 is less severe overall, yet it matters to Node because PFX parsing is actually used there. In real risk assessment, API reachability often matters more than raw CVSS when deciding which systems to fix first. (Datadog Security Labs)
A second useful comparison point is CVE-2022-3602, the OpenSSL X.509 email address buffer overflow from 2022. OpenSSL later explained that pre-announcements had described it as CRITICAL but that further analysis and mitigating factors led to a downgrade to HIGH. The project explicitly mentioned stack protections and platform-specific layout as reasons why remote code execution risk could be lower in practice than the initial headline suggested. That historical example is worth remembering here because it gives engineers a disciplined way to think about stack overflows in OpenSSL: dangerous enough to patch urgently, but still highly sensitive to real execution context. (openssl-library.org)
How to know whether you are actually exposed
The fastest useful exposure workflow is not “find every OpenSSL package.” It is a layered process.
First, identify version presence. You need to know whether affected OpenSSL 3.x branches exist anywhere in your fleet, images, bundled runtimes, appliances, or base containers. OpenSSL’s fixed targets are specific and should drive your package logic. (openssl-library.org)
Second, identify parser reachability. Look for applications and services that do any of the following:
| Exposure indicator | מדוע זה חשוב |
|---|---|
| Accept inbound S/MIME messages | S/MIME commonly relies on CMS structures |
| Decrypt or inspect PKCS#7 / CMS objects | The vulnerable path is in CMS parsing |
| Offer certificate or message import features | User-controlled cryptographic containers are classic parser boundaries |
| Use OpenSSL CMS APIs directly | JFrog identified multiple relevant APIs |
Invoke openssl cms או openssl smime in workflows | CLI use can expose the same parser path |
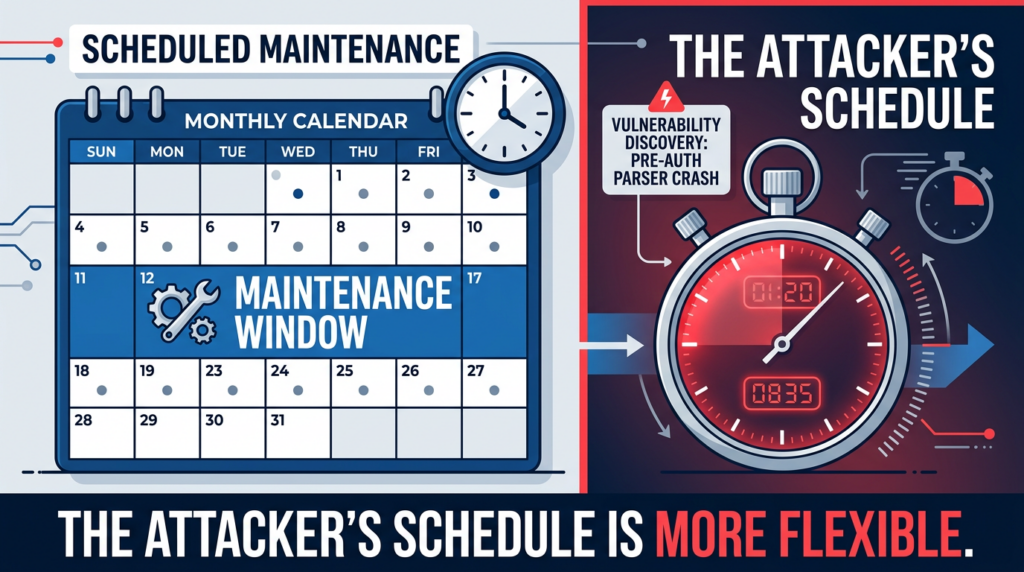
These are the systems that deserve immediate validation, not just package updates during a normal maintenance cycle. (Datadog Security Labs)
Third, check runtime bundling. Datadog explicitly notes that some runtimes package their own OpenSSL version, and that upgrading the OS package alone is not enough in such cases. Node’s January 2026 note is a concrete example of why you need runtime-specific guidance rather than assuming a system package update solves everything. (Datadog Security Labs)
Fourth, confirm with behavior. In a controlled environment, validate that patched builds no longer crash under the known trigger conditions and that your application rejects malformed CMS input safely. Security advisories close tickets; behavioral validation closes uncertainty. (Datadog Security Labs)
Asset and code search patterns that actually help
For source code and repositories, simple patterns can quickly narrow the field:
# code and config search ideas
grep -R "CMS_decrypt" .
grep -R "PKCS7_decrypt" .
grep -R "CMS_EnvelopedData_decrypt" .
grep -R "EVP_CIPHER_asn1_to_param" .
grep -R "openssl cms" .
grep -R "openssl smime" .
grep -R "application/pkcs7" .
grep -R "smime" .
grep -R "p7m" .
For package and host inventory, use the package manager and image metadata rather than relying on ad hoc openssl version checks alone:
# Debian/Ubuntu
dpkg -l | grep -E 'openssl|libssl'
# RHEL/CentOS/Rocky/Alma
rpm -qa | grep -E '^openssl|^openssl-libs'
# Alpine
apk info | grep -E 'openssl|libssl'
# container image layers
syft <image> | grep -i openssl
grype <image> | grep -i CVE-2025-15467
For SBOM-driven environments, the right move is to connect affected version detection with parser-path tagging. A vulnerable package with no CMS exposure path is still debt, but a vulnerable package in a reachable CMS-processing service is urgent debt. (openssl-library.org)
Detection ideas, what you can and cannot expect
There is no magic “CVE-2025-15467 IDS signature” that will save you across every environment. The input is a malformed CMS structure, and the vulnerable boundary often exists inside application logic rather than as a standard HTTP exploit path. Detection therefore tends to come from side effects and workflow-aware instrumentation more than from one universal network signature. (NVD)
What you can monitor includes abnormal process crashes in CMS-processing services, use of openssl cms או openssl smime in unexpected automation paths, inbound S/MIME or PKCS#7 parsing failures clustered around malformed content, and exploit-mitigation alerts such as stack-smashing terminations. Datadog’s example shows a classic *** stack smashing detected *** outcome in the DoS scenario, which is useful as a local validation clue even if it is not a full production detection strategy. (Datadog Security Labs)
A simple Sigma-style hunting idea for Linux process crashes around OpenSSL-driven tooling might look like this:
title: Suspicious OpenSSL CMS or S/MIME Crash Activity
id: 6bba3f1d-2d1c-4d0f-a4b6-cve-2025-15467-demo
status: experimental
logsource:
product: linux
category: process_creation
detection:
selection_img:
Image|endswith:
- '/openssl'
selection_cmd:
CommandLine|contains:
- ' cms '
- ' smime '
condition: selection_img and selection_cmd
level: medium
falsepositives:
- Administrative certificate handling
- Legitimate mail-security tooling
tags:
- attack.t1499
- cve.2025.15467
That is not a canonical detection rule, and it will not find library-linked parser abuse inside custom applications. But it is useful as a starting point in estates where OpenSSL CLI tools appear in server-side workflows and should not be parsing arbitrary inbound content. The stronger long-term answer is application telemetry: log when CMS parsing starts, from what source, under what trust level, and with what failure mode. (Datadog Security Labs)
Patching strategy, when “update OpenSSL” is necessary but not sufficient
The minimum patch action is straightforward: move to the fixed OpenSSL versions for the affected branch, namely 3.6.1, 3.5.5, 3.4.4, 3.3.6, or 3.0.19. That comes directly from OpenSSL’s advisory and vulnerability pages. (openssl-library.org)
But patching is often more complicated in practice for three reasons. First, applications may statically link OpenSSL or bundle their own builds. Second, appliances and commercial products may inherit the vulnerable code through embedded components rather than system packages. Third, downstream vendors may publish their own advisories on different timelines, which can make central vulnerability dashboards look inconsistent for days or weeks after disclosure. That is why version verification must happen at the product and runtime layer, not only at the OS package layer. IBM, Broadcom, Red Hat, AWS, and Fortinet all published downstream material related to CVE-2025-15467, which is a good reminder that the blast radius often travels through supply chains rather than source-only deployments. (Red Hat Customer Portal)
A pragmatic patch priority model looks like this:
| עדיפות | System type | פעולה מומלצת |
|---|---|---|
| P1 | Internet-facing S/MIME gateways, CMS-processing services, external certificate/message import endpoints | Emergency patch and validation |
| P2 | Internal PKI/CA tooling, partner-facing certificate workflows, admin services parsing CMS | Patch urgently and validate exposure |
| P3 | General-purpose servers with affected OpenSSL but no CMS/PKCS#7 reachability | Patch in accelerated maintenance window |
| P4 | Systems on unaffected branches or runtimes with documented non-reachability | Track and document, no panic |
That order reflects reachable parser risk, not just library presence. (Datadog Security Labs)
Where AI-driven validation fits naturally
CVE-2025-15467 is a good example of a class of vulnerability where teams often understand the advisory faster than they can validate exposure. The hard part is usually not reading the CVE. It is answering questions like: Which services actually parse CMS? Which import workflows call OpenSSL directly? Which container images still ship vulnerable 3.x branches? Which environments are reachable from outside trust boundaries? That is where automated asset-aware testing can help, provided the platform is used for verification and scoping, not for theatrical scanning. (Datadog Security Labs)
In a workflow like that, an AI-assisted platform such as Penligent can be useful in two narrow, realistic ways. First, it can help enumerate exposed services, certificate-processing interfaces, and upload boundaries that might accept CMS-like content. Second, it can make validation repeatable by turning the advisory into environment-specific test plans, version checks, and evidence-driven remediation tracking. That is a sensible place for automation. The value is not “AI discovers every OpenSSL bug magically.” The value is cutting down the manual time between disclosure, scope discovery, and proof that the risky parser path is no longer reachable.
A second natural fit is regression testing after patching. When a vulnerability depends on a very specific parser boundary, teams often patch the library but forget to retest the actual business workflow that exposed it in the first place. A platform that can repeatedly exercise those flows, keep notes on which endpoints or services were verified, and store evidence for follow-up audits is far more useful than one more dashboard saying “OpenSSL present.” That is especially true in large organizations where the same cryptographic parsing logic may exist in appliances, old admin tools, and wrapped services nobody thinks about until a CVE lands.
The common mistakes teams will make with CVE-2025-15467
The first mistake is treating every OpenSSL deployment as equally exposed. This creates noise and delays work on the genuinely reachable systems. OpenSSL’s own details and Datadog’s analysis make it clear that reachability depends on CMS or related parsing behavior, not just linkage. (NVD)
The second mistake is overcorrecting and deciding the bug is “not relevant to us” because your web tier only uses HTTPS. That may be true for the web tier and false for your email gateway, certificate import service, S/MIME tooling, or partner integration pipeline. (Datadog Security Labs)
The third mistake is relying on package updates without checking bundled runtimes or product-specific OpenSSL copies. Datadog explicitly warns that upgrading the OS OpenSSL package may not be enough when runtimes package their own versions. (Datadog Security Labs)
The fourth mistake is confusing “no mass exploitation headline yet” with “safe to delay.” Public research already shows a reliable crash and credible RCE potential. That is enough to justify focused remediation where the parser path is exposed. (Datadog Security Labs)
The fifth mistake is writing off the issue because the FIPS module is unaffected. That statement is true, but it only means the vulnerable CMS implementation sits outside the FIPS boundary. It does not mean your application is safe if it still uses the vulnerable non-FIPS parser path. (openssl-library.org)
What a strong remediation note should say internally
A strong internal advisory for this CVE should say something like this:
CVE-2025-15467 is a high-severity OpenSSL stack buffer overflow in CMS (Auth)EnvelopedData parsing. It affects OpenSSL 3.0 before 3.0.19, 3.3 before 3.3.6, 3.4 before 3.4.4, 3.5 before 3.5.5, and 3.6 before 3.6.1. The issue is pre-auth and triggered by malformed CMS input with oversized AEAD IV parameters. Systems are highest priority if they parse untrusted CMS, S/MIME, PKCS#7, or similar content. Standard TLS-only usage is not the primary exposure path. Patch affected branches and validate reachability in all CMS-related workflows. (openssl-library.org)
That summary is short enough for Slack or an incident channel, but specific enough to drive action.
Final assessment
CVE-2025-15467 is exactly the kind of vulnerability that punishes shallow thinking. If you look only at the component name, you will overstate the exposure and flood your teams with noise. If you look only at your primary TLS endpoints, you may miss the real parser surfaces that matter. The right interpretation sits in the middle.
This is a serious OpenSSL vulnerability with a dangerous pre-auth stack corruption primitive, a High vendor severity, and a 9.8 CISA-ADP score. It is not a generic “the internet is burning” bug for every OpenSSL user, but it is a very real problem wherever untrusted CMS or PKCS#7 content reaches the vulnerable parser logic. Public analysis supports reliable denial of service and credible remote code execution potential under the right conditions. The patch targets are clear. The remaining work is environmental: find the real parsing paths, patch the right versions, and validate that the workflows you actually run no longer expose the bug. (NVD)
That is the practical takeaway security teams should keep. Do not treat CVE-2025-15467 as generic OpenSSL panic. Treat it as a message-parsing exposure problem inside OpenSSL. That framing is more accurate, more actionable, and much closer to how this bug will matter in real environments. (NVD)
Suggested internal links and external references
Penligent related reading
- Mongobleed, CVE-2025-14847 Analysis (Penligent)
- CVE-2026-1731 Bomgar, the Remote Support bug you triage like identity infrastructure (Penligent)
- CVE-2023-43208 and the Patch Bypass That Turned Mirth Connect into a High-Priority Internet-Facing RCE (Penligent)
Authoritative external references
- NVD entry for CVE-2025-15467 (NVD)
- CVE record for CVE-2025-15467 (cve.org)
- OpenSSL January 27, 2026 security advisory (openssl-library.org)
- OpenSSL vulnerability page for CVE-2025-15467 (openssl-library.org)
- Datadog Security Labs analysis (Datadog Security Labs)
- JFrog Security Research analysis (JFrog Security Research)
- Node.js OpenSSL security advisory assessment, January 2026 (Node.js)
- OpenSSL background on CVE-2022-3602 (openssl-library.org)