Etiketler: zoneminder v1.37.63 cve, CVE-2024-51482, ZoneMinder SQL injection, ZoneMinder 1.37.65, CCTV security, video surveillance vulnerability, event.php SQL injection, ZoneMinder hardening
If you searched for zoneminder v1.37.63 cve, the answer is not vague, and it is not a bundle of unrelated CVEs. The most relevant vulnerability is CVE-2024-51482, a boolean-based SQL injection issue affecting ZoneMinder v1.37. through 1.37.64*, with the fix landing in 1.37.65. That means ZoneMinder 1.37.63 is affected. GitHub’s official security advisory and NVD say the same thing, and both point to the vulnerable path in web/ajax/event.php. (GitHub)
That direct answer matters because ZoneMinder is not a toy lab application. It is a widely used open-source CCTV and video surveillance platform with a web interface, REST-style API elements, event storage, monitor control, and administrative workflows that often sit close to physical security operations. Its own documentation describes a web/API surface that supports monitors, events, frames, zones, and configuration management, and it exposes live and recorded streams through application endpoints and CGI components. (zoneminder.readthedocs.io)
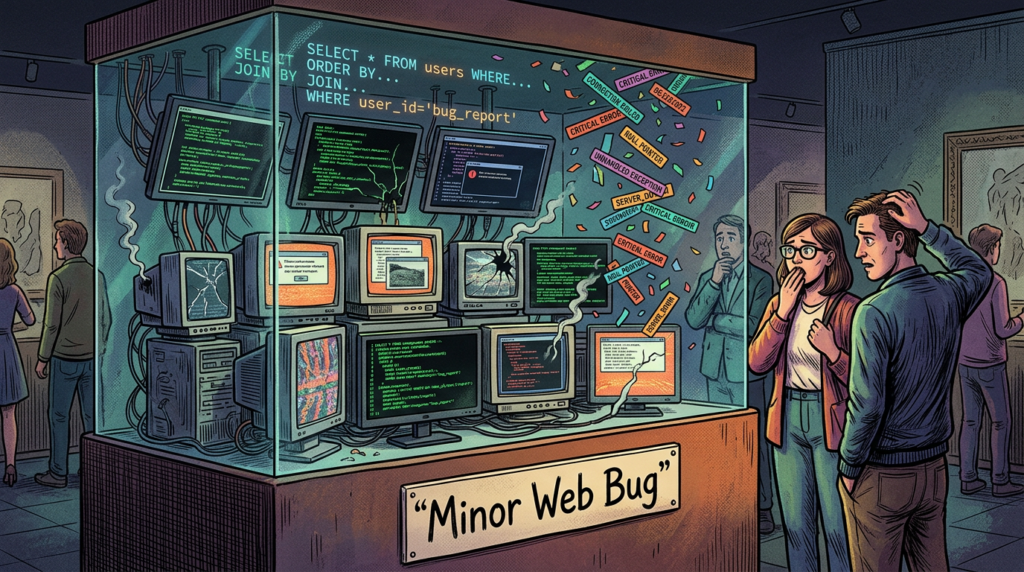
In other words, a SQL injection in ZoneMinder is not just “another web bug.” It is a bug in software that often sits at the boundary between IT, OT-lite environments, facility operations, and incident evidence retention. If an attacker can tamper with event metadata, extract user and monitor data, or pivot from the surveillance management plane into the backend database, the result can affect confidentiality, integrity, and operational trust all at once. OWASP’s SQL injection guidance remains blunt on this point: SQL injection can enable data disclosure, tampering, privilege abuse, and destructive database actions. (OWASP Hile Sayfası Serisi)

The short answer, before the deep dive
Here is the clean conclusion first.
| Question | Answer |
|---|---|
| Is ZoneMinder v1.37.63 affected | Evet |
| Which CVE matters most for this query | CVE-2024-51482 |
| Güvenlik açığı sınıfı | SQL enjeksiyonu |
| Hassas bileşen | web/ajax/event.php |
| Affected range | v1.37.* <= 1.37.64 |
| Fixed version | 1.37.65 |
| Neden önemli | Database compromise risk, event integrity risk, broader admin-plane exposure |
These version facts come directly from the official GitHub advisory and the NVD record. (GitHub)
What CVE-2024-51482 actually is
The official advisory describes the issue as a boolean-based SQL injection içinde web/ajax/event.php. The advisory includes the vulnerable flow in the removetag case, where a request value is read and then inserted directly into a SQL statement. The problem is not exotic. It is the classic pattern OWASP has warned about for years: untrusted input reaches a dynamically constructed SQL query through string concatenation. (GitHub)
GitHub’s advisory shows the issue clearly. In the vulnerable branch, $_REQUEST['tid'] is assigned to $tagId, and that value is later inserted into a SQL string:
- request input enters as
$_REQUEST['tid'] - the code sets
$tagId = $_REQUEST['tid'] - the query is built as
SELECT * FROM Events_Tags WHERE TagId = $tagId - the result count is then used for downstream logic
Because the input was inserted directly into SQL, the query became attacker-influenceable. That is the whole bug. (GitHub)
This matters for two reasons. First, the vulnerable path is not some obscure background daemon unreachable from the web tier; it is in a web-facing AJAX handler. Second, the logic sits in an event-tagging workflow, which is exactly the kind of feature security teams tend to treat as low-risk business logic. In real systems, those are often the routes that escape careful threat modeling.
Why the impact is bigger than “database exposure”
A lot of vulnerability writeups stop at “SQL injection may expose the database.” That is technically correct and operationally incomplete.
ZoneMinder stores the kinds of information attackers value: user data, event metadata, monitor definitions, stream configuration, detection artifacts, and administrative state. Its API documentation shows that the platform is built around operations on monitors, events, frames, zones, and configuration objects. In a surveillance product, even metadata can be operationally sensitive. Which cameras exist, which monitors are enabled, what events fired, what user identities exist, and when recordings happened are all high-value pieces of information in a physical or corporate security context. (zoneminder.readthedocs.io)
OWASP notes that SQL injection commonly leads to disclosure, unauthorized modification, and deletion of data, and in some cases even privilege-related outcomes if authentication or authorization data lives in the same database. That warning is especially relevant here. In a surveillance environment, an attacker may not need flashy code execution to cause real harm. Changing event state, altering tags, corrupting historical records, or enumerating cameras and users may be enough to degrade trust in the system or support a larger intrusion. (OWASP Vakfı)
A modern security team should think about three layers of impact:
First, confidentiality. Event metadata, camera inventory, user data, network naming conventions, and potentially authentication-relevant records may all become exposed if the SQLi can enumerate backend tables. OWASP explicitly identifies disclosure as one of the most common outcomes of SQL injection. (OWASP Vakfı)
Second, integrity. In a CCTV system, integrity is often more important than uptime. If event-related records are modified, if tags are deleted or altered, or if downstream analytics consume corrupted event history, the system may still be online while its evidentiary value is compromised. That is a serious operational problem, not just an AppSec finding. (GitHub)
Third, lateral consequence. Even when a SQL injection does not directly become OS-level compromise, the exposed information may help attackers chain into broader access. ZoneMinder’s own documentation discusses auth tokens, API use, live stream controls, and integration workflows. That makes the admin plane a useful foothold for follow-on operations if the deployment is poorly segmented. (zoneminder.readthedocs.io)
The version story matters more than many teams realize
One of the easiest mistakes defenders make with ZoneMinder is assuming that “newer 1.37” automatically means “secure enough.” The public record shows a more fragmented reality.
Bu zoneminder v1.37.63 cve query is not only about one bug. It reflects a broader pattern in the 1.37 line. NVD records show that:
- CVE-2024-43359 was a cross-site scripting issue fixed in 1.37.61. (NVD)
- CVE-2024-43360 was a time-based SQL injection issue also fixed in 1.37.61. (NVD)
- CVE-2024-51482 remained present through 1.37.64 and was fixed only in 1.37.65. (GitHub)
So an operator who upgraded to 1.37.61 may have closed one cluster of issues but still remained exposed to another serious SQL injection until moving to 1.37.65. That is exactly why version pinning without vulnerability mapping is dangerous.
This is the practical patch matrix:
| Versiyon | CVE-2024-43359 | CVE-2024-43360 | CVE-2024-51482 | Security posture summary |
|---|---|---|---|---|
| 1.37.60 and older | Savunmasız | Savunmasız | Vulnerable if within affected 1.37 range before 1.37.65 | Poor |
| 1.37.61 | Fixed for 43359 | Fixed for 43360 | Still vulnerable | Incomplete |
| 1.37.63 | Fixed for 43359 | Fixed for 43360 | Savunmasız | Still exposed |
| 1.37.64 | Fixed for 43359 | Fixed for 43360 | Savunmasız | Still exposed |
| 1.37.65 | Fixed | Fixed | Fixed | Recommended baseline within 1.37 |
The source for those version boundaries is the public NVD and GitHub advisory trail. (GitHub)
This is not an isolated ZoneMinder episode
If you only read the current advisory, CVE-2024-51482 can look like a one-off coding mistake. The broader ZoneMinder vulnerability history suggests something more important: the management plane has repeatedly been a security risk surface.
In 2023, CVE-2023-26035 exposed an unauthenticated remote code execution path caused by missing authorization around snapshot handling. NVD states that versions prior to 1.36.33 ve 1.37.33 were vulnerable, and the vulnerable flow eventually reached shell_exec via attacker-supplied input. (NVD)
In the same time frame, CVE-2023-26038 affected versions prior to 1.36.33 ve 1.37.33 with a local file inclusion issue in web/ajax/modal.php, allowing an arbitrary PHP file path to be passed and loaded. (NVD)
Then in 2024, ZoneMinder saw additional web-plane flaws, including CVE-2024-43360 for SQL injection and CVE-2024-43359 for XSS, both fixed in 1.37.61. (NVD)
Taken together, those issues tell a more useful story than any single CVE page can. The risk is not just “upgrade for this advisory.” The real lesson is that ZoneMinder deployments should be treated as exposed, high-value administrative applications and engineered accordingly. If your program still treats them as low-priority facility tools, you are underestimating the blast radius.
What the vulnerable code tells us about engineering quality
The most useful thing about CVE-2024-51482 is not its CVSS label. It is what the bug reveals about secure coding practice.
GitHub’s advisory shows that the vulnerable code trusted a request parameter and embedded it directly into a query. OWASP’s prevention guidance says the remedy is not clever escaping and not a WAF-only bandage. The first-line fix is to stop building SQL dynamically with user input and instead use parameterized queries and validated input handling. OWASP’s language is unambiguous on this point. (GitHub)
A simplified secure rewrite looks like this:
<?php
// Illustrative safer pattern, not copied from production source
$tagId = filter_input(INPUT_POST, 'tid', FILTER_VALIDATE_INT);
$eventId = filter_input(INPUT_POST, 'id', FILTER_VALIDATE_INT);
if ($tagId === false || $eventId === false) {
http_response_code(400);
exit('Invalid input');
}
$sql = 'SELECT * FROM Events_Tags WHERE TagId = ?';
$rowCount = dbNumRows($sql, [$tagId]);
if ($rowCount < 1) {
$deleteSql = 'DELETE FROM Tags WHERE Id = ?';
$response = dbNumRows($deleteSql, [$tagId]);
ajaxResponse(['response' => $response]);
}
?>
That code block is illustrative, but the defensive principle is exactly aligned with OWASP’s guidance: parameterize, validate, and avoid direct string concatenation with untrusted input. (OWASP Hile Sayfası Serisi)
The deeper engineering lesson is this: in surveillance software, “minor” convenience routes such as tag management, playback filters, modal views, and snapshot actions should be assumed hostile. These are precisely the endpoints attackers love because product teams often give their hardest review effort to the login page, not to asynchronous event actions.
How defenders should interpret exploitability
The public advisory lists the issue as Kritik, and the NVD record carries the GitHub-supplied vector showing network attackable, low complexity, no user interactionve high impact on confidentiality, integrity, and availability, with low privileges required. That privilege requirement matters: this is not described as a totally unauthenticated internet worm bug, but it is still severe because many ZoneMinder deployments are weakly segmented, shared among multiple roles, or reachable from semi-trusted internal users and service accounts. (GitHub)
That distinction is operationally important. Some teams wrongly translate “PR:L” into “low priority.” In real environments, low privilege often means:
- any valid operator account
- any compromised helpdesk or monitoring account
- any stale contractor credential
- any pivot from another internal foothold
- any integration account with broader access than intended
For a surveillance management system, that is more than enough to matter.
Where exposure usually comes from in the real world
ZoneMinder’s own documentation and wiki contain a subtle but important warning: authentication exists, but authenticated mode alone should not be relied on for securing internet-connected ZoneMinder, and enabling built-in authentication is highly recommended unless another secure method protects access. The documentation also warns against putting credentials directly in URLs because they may appear in logs. (zoneminder.readthedocs.io)
That maps closely to how surveillance deployments actually go wrong:
- the web UI is exposed to the internet for convenience
- legacy reverse proxies forward too much
- authentication is enabled, but with weak segmentation
- API and stream endpoints leak through broad allow rules
- old versions remain in package repos or manual builds
- internal-only assumptions turn into public exposure after a firewall or NAT change
ZoneMinder’s downloads page even cautions Ubuntu users that default distro repositories can be out of date and recommends the maintained PPA path instead. For defenders, that is a reminder that “we installed it from the repo” is not a patch management strategy. (ZoneMinder)
What to do right now if you run ZoneMinder 1.37.63
The first action is still the simplest one: upgrade to 1.37.65 or later within the supported line you use. Both the advisory and NVD are explicit that 1.37.65 is the fix for CVE-2024-51482. (GitHub)
The second action is just as important: treat the web application as a protected admin plane, not a public service. ZoneMinder documentation states plainly that authenticated mode alone is not enough for internet-connected deployments. Put the UI behind VPN, IP allowlisting, or a tightly controlled reverse proxy. (zoneminder.readthedocs.io)
The third action is to audit for signs of historical abuse, especially if you were on 1.37.63 or 1.37.64 for any meaningful period. Even without confirmed widespread exploitation, the vulnerability class is mature and attractive. Look for abnormal requests to event-related endpoints, suspicious tag operations, unexplained event metadata anomalies, unexpected DB reads, and admin-plane access from unusual sources. That is a risk-based inference from the vulnerability type and exposed path; it is not a claim of confirmed mass exploitation. The official public sources establish the flaw and the endpoint, which is enough to justify a retrospective review. (GitHub)
A practical hardening checklist
Use this as an engineering baseline, not just a compliance checkbox.
| Kontrol | Neden önemli | Öncelik |
|---|---|---|
| Upgrade to 1.37.65 or later | Removes the known vulnerable path for CVE-2024-51482 | Hemen |
| İnternete maruz kalmayı kısıtlayın | Reduces attack surface against admin endpoints | Hemen |
| Enable authentication | Necessary baseline control | Hemen |
| Do not rely on auth alone | Official docs warn it is insufficient for internet-connected systems | Hemen |
| Put ZoneMinder behind VPN or IP allowlist | Limits who can reach the UI and AJAX endpoints | Yüksek |
| Review DB privileges | Limits post-SQLi blast radius | Yüksek |
| Inspect access logs and DB activity | Helps identify prior misuse | Yüksek |
Review reverse proxy rules for /zm and related paths | Prevents overly broad access to admin and AJAX routes | Yüksek |
| Re-check package source freshness | Avoids stale distro packages | Orta |
| Segment surveillance infrastructure from core business systems | Contains fallout | Yüksek |
These recommendations align with the fix information in the advisory, the ZoneMinder auth guidance, and OWASP’s SQL injection prevention principles. (GitHub)
Safe validation steps, without turning this into an exploitation guide
A lot of teams either stop at reading the CVE page or go too far into unsafe reproduction. There is a better middle ground: validate exposure, version, reachability, and remediation without destructive testing.
1. Confirm the installed version
zm --version 2>/dev/null || zoneminder --version 2>/dev/null || dpkg -l | grep -i zoneminder
If the result is 1.37.63 veya 1.37.64, you should assume exposure to CVE-2024-51482 until upgraded. That mapping comes from the advisory and NVD. (GitHub)
2. Check whether the admin plane is externally reachable
curl -I <https://your-zoneminder.example.com/zm/>
curl -I <https://your-zoneminder.example.com/zm/index.php>
This does not test the vulnerability. It simply confirms whether the management interface is reachable from the network path you are checking.
3. Verify that authentication is actually enforced
curl -s -o /dev/null -w "%{http_code}\\n" <https://your-zoneminder.example.com/zm/index.php>
A 200 from an untrusted origin may indicate broader exposure than intended. Whether that is acceptable depends on your architecture, but the official docs are clear that unauthenticated or broadly reachable modes require other strong protections. (zoneminder.readthedocs.io)
4. Validate post-patch behavior at the change-management level
After upgrading, confirm:
- package/version changed
- reverse proxy and service restarted cleanly
- logs show no recurring application errors
- event management UI still functions normally
- no exception traces appear around event or tag operations
5. Review the database account model
Even though patching is the priority, OWASP emphasizes least privilege as an important secondary defense. The app’s DB account should not have broader rights than the application truly needs. If SQL injection happens anywhere in the stack, database least privilege can sharply reduce damage. (OWASP Hile Sayfası Serisi)
Example reverse-proxy restrictions
A clean defensive pattern is to deny broad public access and only allow trusted management networks.
server {
listen 443 ssl http2;
server_name zm.example.com;
location /zm/ {
allow 10.0.0.0/8;
allow 192.168.0.0/16;
deny all;
proxy_pass <http://127.0.0.1:8080>;
proxy_set_header Host $host;
proxy_set_header X-Forwarded-For $remote_addr;
proxy_set_header X-Forwarded-Proto https;
}
}
This is not a substitute for patching. It is a compensating control that reduces reachability.

ZoneMinder v1.37.63 CVE — The Vulnerability Security Teams Are Actually Looking For
Detection ideas security teams can operationalize
Because CVE-2024-51482 is tied to a web-facing event action, defenders should watch for anomalies around event-management requests, especially unusual patterns hitting view=request, request=event, or tag-manipulation flows. The official advisory identifies the vulnerable action path and parameter context, which is enough to justify targeted logging and detection around those routes. (GitHub)
A lightweight HTTP log hunting approach might look like this:
grep -E 'view=request|request=event|action=removetag|/zm/index.php' /var/log/nginx/access.log
That command is a starting point for defenders, not a complete analytic. In production, you would want to normalize and review:
- source IP
- kimliği doğrulanmış kullanıcı
- unusual request rates
- rare parameter combinations
- repeated errors or DB-related failures
- requests from networks that should never administer cameras
If you are using a SIEM, create an analytic for event-action routes reached from untrusted or unexpected source ranges, especially outside normal maintenance windows.
Why CCTV software deserves a different threat model
The biggest mistake organizations make with software like ZoneMinder is cultural. They treat it like “just another internal web app.” It is not.
A surveillance management platform sits at the junction of video evidence, physical monitoring, privileged administration, and sometimes long-lived operational workflows. A compromise may affect not only IT assets but also investigations, access disputes, safety reviews, workplace incidents, or legal evidence quality. That is why the integrity dimension matters so much here. OWASP’s generic SQL injection consequences become much more concrete when the underlying records are security events and camera metadata rather than product catalog rows. (OWASP Vakfı)
The broader ZoneMinder CVE history reinforces that point. When a product line has seen LFI, unauthenticated RCE, XSS, and multiple SQL-related flaws across adjacent versions, the right response is not just “apply this patch and move on.” The right response is to raise the overall trust boundary around the platform. (NVD)
For a vulnerability like this, the hard part is often not reading the advisory. The hard part is answering four operational questions with confidence:
- Which assets are actually running the vulnerable version
- Which of them are externally or broadly reachable
- Which routes are really exposed behind reverse proxies and auth layers
- Whether the fix actually removed the risk in the live environment
That is the part of the workflow where automated validation becomes more valuable than generic scanning. A modern AI-assisted testing platform can help security teams map exposure, verify version and route reachability, test whether compensating controls hold, and reduce the gap between “patch announced” and “risk truly closed.” Penligent’s public material frames this as moving from tool-by-tool scripting toward evidence-driven, automated penetration testing, including validation workflows around web vulnerabilities and WAF-protected paths. (Penligent)
That is especially relevant for products like ZoneMinder, where a single CVE page does not tell you whether your deployment is reachable through legacy routing, whether an internal-only assumption still holds, or whether a patch left adjacent admin routes too open. In practice, the organizations that close risk fastest are not the ones that read advisories first. They are the ones that can verify exposure and remediation fastest.
Final verdict
If your question is simply, “Is there a CVE for ZoneMinder v1.37.63,” the most important answer is yes — CVE-2024-51482. ZoneMinder 1.37.63 is in scope, the flaw sits in web/ajax/event.php, and the public fix is 1.37.65. (GitHub)
If your question is the more useful one — “What should a serious security team conclude from that” — the answer is bigger:
- patch immediately
- assume the management plane is high value
- do not expose the UI broadly
- do not rely on auth alone
- review database privilege boundaries
- audit for historical misuse
- treat ZoneMinder as part of your security-critical infrastructure, not as an afterthought
That conclusion is not based on one scary headline. It follows directly from the advisory, the NVD records, ZoneMinder’s own auth guidance, and the platform’s recent vulnerability history. (GitHub)
Daha Fazla Okuma
- NVD entry for CVE-2024-51482: (NVD)
- Official GitHub advisory for CVE-2024-51482: (GitHub)
- ZoneMinder downloads and package guidance: (ZoneMinder)
- ZoneMinder API documentation: (zoneminder.readthedocs.io)
- ZoneMinder authentication guidance: (zoneminder.readthedocs.io)
- OWASP SQL Injection Prevention Cheat Sheet: (OWASP Hile Sayfası Serisi)
- OWASP SQL Injection overview: (OWASP Vakfı)
- The Rise of Autonomous Hacking: How AI Pentest Tools Are Rewriting Security: (Penligent)
- The 2026 Ultimate Guide to AI Penetration Testing: (Penligent)
- Scripting in Cybersecurity, From Scripting to Automating Penetration Testing: (Penligent)
- The Art of Bypassing WAFs, and How Penligent Brings Safe Automated Validation: (Penligent)
- PentestGPT vs. Penligent AI in Real Engagements: (Penligent)