Most vulnerability write-ups collapse into one of two bad habits. They either dramatize every fresh CVE as the next industry-wide catastrophe, or they flatten it into a sterile summary that tells defenders almost nothing about how to prioritize it. CVE-2026-21385 deserves neither treatment.
What makes this vulnerability matter is not that it carries the highest possible score. It does not. What makes it matter is the combination of four facts that are now publicly established. First, the official record describes it as a Qualcomm memory-corruption issue tied to memory-allocation alignment handling and maps it to CWE-190, integer overflow or wraparound. Second, Google’s March 2026 Android Security Bulletin says there are indications it “may be under limited, targeted exploitation.” Third, the flaw is included in the 2026-03-05 Android patch level rather than the lighter 2026-03-01 set, which already tells you something about where it sits in the monthly patch structure. Fourth, CISA added it to the Known Exploited Vulnerabilities catalog on March 3, 2026, with a federal remediation due date of March 24. (NVD)
That changes the conversation. CVE-2026-21385 is not interesting because it is flashy. It is interesting because it lives at the intersection of mobile endpoint risk, chipset supply chain complexity, Android patch fragmentation, and targeted exploitation. For security teams, that combination is operationally expensive. A Windows server CVE often produces a familiar workflow: inventory, patch, scan, validate. Android and Qualcomm vulnerabilities force a more awkward reality. You are not patching one vendor’s software on one standardized fleet. You are dealing with Google, Qualcomm, device OEMs, carriers in some cases, mixed Android versions, and users who may not install updates promptly even when the patch exists. That is why this bug should be treated as an incident-management problem, not merely a vulnerability-management ticket. (Android Open Source Project)
The official description is compact: “Memory corruption while using alignments for memory allocation.” Qualcomm supplied a CVSS v3.1 vector of AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H, which yields a 7.8 High score, and NVD shows the associated weakness as CWE-190. In plain English, the public record points to arithmetic or size-handling logic around allocation alignment that can produce memory corruption when assumptions break. Qualcomm’s March 2026 bulletin characterizes the issue as an integer overflow or wraparound in Graphics, while Android’s March 2026 bulletin places CVE-2026-21385 in the 2026-03-05 section under Qualcomm-related display components. (NVD)
That wording matters because it tells us what we can responsibly say and what we cannot. We can say the bug class is consistent with alignment-sensitive arithmetic producing invalid size outcomes, under-allocation, or other unsafe memory states. We can say memory corruption in graphics or display-adjacent paths has historically been dangerous because these paths are performance-sensitive, widely reachable by complex inputs, and often embedded in exploit chains rather than used alone. We cannot honestly claim a full public exploit path, a weaponized PoC, or a definitive attack chain from the currently disclosed sources. Public coverage repeatedly notes targeted exploitation, but the official advisories do not publish exploitation specifics. Any article that pretends otherwise is doing fiction, not engineering. (NVD)
What CVE-2026-21385 Actually Is
At the record level, CVE-2026-21385 is a Qualcomm vulnerability described as memory corruption while using alignments for memory allocation. NVD lists Qualcomm as the source, preserves Qualcomm’s CVSS v3.1 score of 7.8 High, and records the weakness as CWE-190. CVE.org reflects the same base description. Android’s March 2026 bulletin includes the issue in the 2026-03-05 patch level and notes that there are indications of limited, targeted exploitation. CISA’s KEV status means this is no longer just a vendor bulletin issue; it is part of the U.S. government’s actively exploited tracking and remediation workflow. (NVD)
The most disciplined way to interpret the public record is this: CVE-2026-21385 is a local-attack-vector Qualcomm memory-corruption flaw in the Android ecosystem, severe enough to warrant High scoring, serious enough for Google to call out possible live targeted exploitation, and important enough for CISA to elevate into KEV immediately after disclosure. That is already enough to justify emergency prioritization for organizations with Android fleets, executive mobile users, field devices, corporate BYOD exposure, or mobile access to sensitive SaaS and internal systems. (NVD)
Some public summaries describe the vulnerable area as a graphics component, while Android’s bulletin labels the subcomponent as Display. Those are not contradictions so much as they are reminders that Android security disclosure often compresses layered component details into vendor-specific groupings. SecurityWeek, CyberScoop, TechRadar, and other contemporaneous coverage all converge on the same operational picture even if wording differs slightly: this is a Qualcomm component issue in Android’s March 2026 patch cycle, it affects a very broad hardware surface, and the exploitation warning should be taken seriously. (SecurityWeek)
Why the CVSS Score Understates the Real Problem
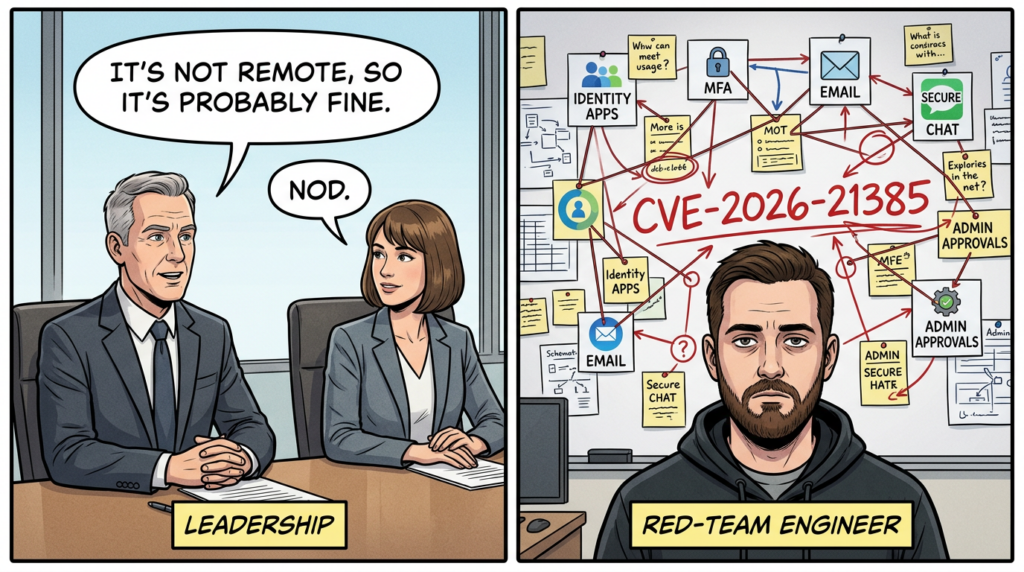
There is a persistent bad habit in security teams that do not spend much time on mobile: if a vulnerability is not remote, they mentally demote it. That shortcut is dangerous here.
The CVSS vector for CVE-2026-21385 is local. On paper, that may sound less urgent than the critical remote code execution issues sitting elsewhere in the same Android bulletin. In practice, “local” on Android does not mean harmless. It means the flaw is not, by itself, a one-packet remote compromise. But real mobile attacks are often chained. Attackers do not need every stage to be remotely reachable if they can land code execution, process-level footholds, or malicious app presence by some other means and then move into more privileged or more stable territory. That is why limited, targeted exploitation matters so much more than a simplistic reading of AV:L. (NVD)
This is especially true in the modern Android threat model. High-value users do not primarily lose devices through commodity smash-and-grab malware. They are more likely to be hit through narrow, selective chains that focus on persistence, surveillance, credential access, message collection, microphone or camera access, or data theft from apps that already hold the user’s trust. Public reporting around CVE-2026-21385 repeatedly frames the exploitation context as targeted rather than opportunistic. Dark Reading explicitly raises the possibility of commercial spyware or nation-state activity. That remains an inference, not an officially confirmed attribution, but it is a credible one because limited, targeted exploitation is exactly the language you expect when a vendor is acknowledging real-world abuse without disclosing operational details. (Android Open Source Project)
The right lesson for defenders is not “this is spyware for sure.” The right lesson is more practical: if your risk model includes executives, journalists, researchers, legal teams, politicians, regulated industry leaders, or employees with access to sensitive corporate messaging and identity systems, then a locally exploitable Android vulnerability with confirmed targeted activity belongs in your urgent-response lane. That is true even before public exploit details emerge. (Android Open Source Project)
What Is Officially Confirmed and What Is Still Inference
A good technical article should separate evidence from narrative. Here is the evidence line.
Officially confirmed: Qualcomm disclosed CVE-2026-21385 as a memory-corruption issue related to alignment during memory allocation and tied it to CWE-190. NVD records Qualcomm’s 7.8 High score and preserves that description. Android’s March 2026 Security Bulletin includes the flaw in the 2026-03-05 security patch level and explicitly states there are indications it may be under limited, targeted exploitation. CISA added the CVE to the KEV catalog on March 3, 2026, with a due date of March 24 for U.S. federal civilian agencies. Android’s bulletin also states that devices on patch level 2026-03-05 or later address all issues in that patch set and all previous patch levels. (NVD)
Still inference: whether the exploitation has been used by a specific spyware vendor, whether a browser or messaging exploit chain was involved, whether the vulnerability leads to code execution in all realistic conditions, and whether public exploit primitives will emerge soon. These claims may turn out to be true, but none of them are established by the primary sources. Some reputable reporting suggests likely advanced-threat usage, but that still belongs in the “plausible interpretation” bucket, not the “confirmed fact” bucket. (Karanlık Okuma)
That distinction matters because overclaiming damages trust. It also creates bad operational habits. Teams that act only when full exploit details are public are often late. Teams that treat every rumor as a completed attack chain burn time and attention. The right middle ground is to act decisively on what is verified, while keeping the hypothetical parts clearly labeled. CVE-2026-21385 easily clears that threshold for urgent action. (NVD)

How Broad Is the Exposure
One of the hardest things about Qualcomm and Android security events is that the risk is not limited to one brand headline. It travels through chipsets, OEM builds, update schedules, and device populations that do not all move together.
Public reporting around the March bulletin describes the vulnerable surface as spanning more than 200 Qualcomm chipsets, with reputable summaries citing either 234 or 235 depending on the source. Because that minor count discrepancy appears in secondary reporting rather than the short Android bulletin text itself, the most careful way to phrase it is that the issue affects a very large Qualcomm hardware footprint, not a niche or boutique subset. CyberScoop reports 234 chipsets based on Qualcomm’s security bulletin, while other reports summarize the affected scope as 235. The exact number matters less than the planning consequence: this is broad mobile ecosystem exposure, not a single-device edge case. (CyberScoop)
For enterprise defenders, exposure should be thought of in layers. The first layer is corporate-managed Android. If your MDM or EMM stack allows you to see model, OEM, patch level, and device compliance status, you can usually turn this into a measurable fleet action. The second layer is BYOD, which is always messier because patch lag, device diversity, and privacy boundaries limit visibility. The third layer is unmanaged high-risk mobile access: contractors, overseas field staff, third-party support personnel, or operational personnel using Android devices for privileged access to cloud consoles, VPN, admin panels, secure chat, or corporate email. That third layer is often the one organizations forget until after an incident. (CyberScoop)
The other hard truth is Android fragmentation. Google publishes the bulletin, Qualcomm provides fixes to device makers, but end-user protection depends on OEM rollout and user installation. That creates a delay between “patch exists” and “risk materially reduced.” Public coverage of the March 2026 bulletin emphasizes this fragmentation problem, noting that Pixel users typically receive updates faster, while the rest of the ecosystem depends on manufacturer integration schedules. (TechRadar)
The March 2026 Android Bulletin Context Matters
Defenders should not look at CVE-2026-21385 in isolation because Google’s March 2026 Android bulletin is not a one-bug story. It is a large monthly release that addresses 129 vulnerabilities, including multiple critical issues. The bulletin itself highlights that the most severe issue in the System section, CVE-2026-0006, could lead to remote code execution with no additional privileges and no user interaction. The Framework section includes a critical elevation-of-privilege flaw, CVE-2026-0047. The System section also includes a critical denial-of-service issue, CVE-2025-48631. The 2026-03-05 patch level further includes critical kernel and hypervisor issues such as CVE-2026-0037 and CVE-2026-0038. (Android Open Source Project)
This wider context changes how mature teams should respond. If you are already mobilizing because of CVE-2026-21385, the most efficient response is not a single-CVE communication. It is a March Android emergency patch message tied to patch level 2026-03-05 or later, with specific emphasis on the exploited Qualcomm issue but explicit recognition that the bulletin also closes other serious pathways. That reduces the risk of “patch myopia,” where teams overfocus on the exploited headline and underreact to the critical but less publicized vulnerabilities in the same release. (Android Open Source Project)
This is also why downstream verification matters. A device reporting that it is “updated recently” is not enough. The Android bulletin is precise: 2026-03-05 or later is the patch level that covers the 2026-03-05 set and all previous patch levels. If your mobile fleet still sits at 2026-03-01, then from the bulletin’s perspective you are not done. (Android Open Source Project)

A Practical Technical Model of the Bug Class
Without inventing exploit details, we can still explain the engineering pattern in a useful way.
Alignment handling shows up when software needs memory blocks to satisfy hardware or performance constraints. Instead of simply allocating size bytes, code often rounds the requested value up to some alignment boundary, such as 8, 16, 64, or page-sized units. If those calculations use the wrong integer type, fail to validate bounds, or assume the rounded result will always remain larger and valid, overflow or wraparound can occur. That can produce a value smaller than expected, cause an undersized allocation, or desynchronize the relationship between requested size and actual buffer length. Once the software continues under the false assumption that the buffer is large enough, subsequent reads or writes can corrupt memory. Qualcomm’s own classification of the bug as an integer overflow or wraparound aligns with that general pattern. (Qualcomm Docs)
A minimal conceptual example looks like this:
size_t aligned = (user_len + alignment - 1) & ~(alignment - 1);
void *buf = malloc(aligned);
memcpy(buf, input, user_len);
At first glance this looks routine. But if user_len + alignment - 1 overflows, or if the types involved truncate unexpectedly, aligned may become smaller than intended. The malloc succeeds, but the subsequent copy or downstream parser assumes the original logical size is safe. That gap is where memory corruption begins.
A more defensive version tends to look like this:
bool align_up_checked(size_t user_len, size_t alignment, size_t *out) {
if (alignment == 0) return false;
if ((alignment & (alignment - 1)) != 0) return false; // power of two
if (user_len > SIZE_MAX - (alignment - 1)) return false;
size_t candidate = (user_len + alignment - 1) & ~(alignment - 1);
if (candidate < user_len) return false;
*out = candidate;
return true;
}
This does not tell us Qualcomm’s exact implementation, but it illustrates the class of failure accurately: arithmetic around alignment is easy to get subtly wrong, and subtle arithmetic bugs in low-level, performance-sensitive, graphics-adjacent code can have severe consequences. (Qualcomm Docs)
In mobile exploitation, graphics and display paths deserve special respect. They are close to memory-heavy operations, often interact with complex driver and firmware boundaries, and may be reached by richly structured content. Even when a flaw is not directly remote, the surrounding subsystem often sits in places where exploit developers look for post-entry leverage. That does not prove a specific chain here, but it does explain why defenders should not casually dismiss a Qualcomm display or graphics memory-corruption issue as a “mere local bug.” (Android Open Source Project)
A Table Security Teams Can Actually Use
| Question | What the public record supports | Neden önemli |
|---|---|---|
| Is CVE-2026-21385 real and officially assigned? | Yes. CVE.org and NVD both list it. (CVE) | No ambiguity about the identifier. |
| Is it actively exploited? | Google says there are indications it may be under limited, targeted exploitation. CISA added it to KEV. (Android Open Source Project) | This moves it into urgent-response territory. |
| What is the bug class? | Memory corruption tied to alignment in memory allocation, mapped to CWE-190. (NVD) | Helps frame realistic failure modes. |
| Is it remote code execution by itself? | Not established by the primary sources. CVSS vector is local. (NVD) | Avoids overstating exploitability. |
| Which Android patch level matters? | 2026-03-05 or later. (Android Open Source Project) | The difference between partially and fully patched matters here. |
| Is this just one bug in a quiet month? | No. March 2026 patched 129 Android vulnerabilities, including multiple critical issues. (Android Open Source Project) | Teams should treat the month’s update holistically. |
| Does affected scope look narrow? | No. Public reporting describes over 200 affected Qualcomm chipsets. (CyberScoop) | Asset scoping should assume broad exposure. |
What Security Teams Should Do in the First 24 Hours
The first task is not malware hunting. It is exposure clarification.
Pull an Android device inventory with at least these fields: user, business role, management status, OEM, model, Android version, current security patch level, corporate app access, and whether the device is allowed to access high-value systems. If your tooling cannot answer those questions for Android, that is not a CVE-2026-21385 problem. That is a mobile security program problem that this CVE is exposing. (Android Open Source Project)
Next, identify three priority groups. The first group is high-value people: executives, security engineers, legal, deal teams, journalists, researchers, activists, or anyone likely to be a deliberate target. The second group is high-privilege devices: phones used for SSO, password manager access, incident response coordination, administrative messaging, or MFA for sensitive systems. The third group is patch-lagging Android devices from OEMs with historically slower update cadence. Those three groups should receive separate handling, not a single generic “please update your phone” message. (Android Open Source Project)
Then issue a patch directive keyed to the Android security patch level, not vague language like “latest update.” You want a measurable condition: patch level 2026-03-05 or later. If your MDM can enforce compliance gates, use them. If it cannot, at least require attestation and collect evidence. The Android bulletin is clear about what patch level closes the full March 2026 set. (Android Open Source Project)
Finally, assume a temporary threat posture change. Because the exploitation note is real but technical detail is limited, it makes sense to tighten mobile risk around sideloading, app installation permissions, debugging exposure, and access to the most sensitive internal resources until patch status becomes visible. That is a rational precaution, not panic. (Android Open Source Project)

What to Do in the First 72 Hours
By 72 hours, the goal shifts from messaging to evidence.
First, verify which devices actually reached 2026-03-05 or later. This sounds obvious, but many organizations stop at vendor-announcement awareness rather than actual compliance measurement. For Android, those are not the same thing. A bulletin can be public while a large portion of your fleet remains effectively vulnerable because of OEM lag, user delay, or unmanaged devices. (Android Open Source Project)
Second, review whether any high-risk users remain on older patch levels. Those users should trigger individual outreach and, in some environments, temporary access controls. If a device used by privileged personnel cannot be updated promptly, you may need compensating controls such as limiting certain admin workflows from mobile, enforcing stronger conditional access, or routing sensitive work to hardened endpoints until the mobile risk window closes. (Android Open Source Project)
Third, correlate mobile patch status with identity risk. Android vulnerabilities do not matter only to the phone. They matter because the phone is often the user’s identity broker: email, authenticator, SSO approvals, password managers, cloud-console notifications, secure chat, and corporate documents all sit there. A targeted mobile compromise is often less about the device and more about what the device can unlock. That is why mobile exposure should be reviewed alongside high-privilege SaaS accounts and incident-response communications channels. (Karanlık Okuma)
Detection and Verification Workflows
There is no public IOC set for CVE-2026-21385 exploitation in the primary sources I reviewed. That means defenders should not pretend there is a neat signature-based answer. What you can do, however, is improve patch verification and narrow the window where an attacker could benefit.
For hands-on validation in controlled environments, the simplest baseline check is patch level collection via ADB for test devices:
#!/usr/bin/env bash
set -euo pipefail
adb devices | awk 'NR>1 && $2=="device" {print $1}' | while read -r serial; do
patch_level=$(adb -s "$serial" shell getprop ro.build.version.security_patch | tr -d '\\r')
model=$(adb -s "$serial" shell getprop ro.product.model | tr -d '\\r')
manufacturer=$(adb -s "$serial" shell getprop ro.product.manufacturer | tr -d '\\r')
echo "$serial | $manufacturer | $model | patch=$patch_level"
done
If you need a quick compliance gate for lab verification, even a rough shell check is better than vague status assumptions:
required="2026-03-05"
adb devices | awk 'NR>1 && $2=="device" {print $1}' | while read -r serial; do
patch_level=$(adb -s "$serial" shell getprop ro.build.version.security_patch | tr -d '\\r')
if [[ "$patch_level" < "$required" ]]; then
echo "[NONCOMPLIANT] $serial patch=$patch_level"
else
echo "[OK] $serial patch=$patch_level"
fi
done
For fleet-level governance, the better model is to pull patch level, device model, and management state from MDM or EMM into a compliance table and separate results into four buckets: compliant managed, noncompliant managed, visible unmanaged, and unknown. Unknown is not a neutral bucket. In real incidents, unknown often becomes the problem set. The bulletins give you the target state; your tooling has to prove you reached it. (Android Open Source Project)
You should also review enterprise Android policies around sideloading, USB debugging, app-source restrictions, and Play Protect posture. Google’s bulletin notes broader platform mitigations and Google Play Protect as part of Android’s defensive posture, and while those mitigations do not replace patching, they do reduce the chance that opportunistic or adjacent attack stages succeed. (Android Open Source Project)
Related CVEs You Should Mention in the Same Briefing
Security leaders hate fragmented reporting, and with good reason. If you brief them only on CVE-2026-21385, you are telling a true story too narrowly.
A more complete March 2026 Android briefing should include CVE-2026-0006, because Android’s bulletin labels it the most severe issue in the System section and says it could lead to remote code execution without additional privileges or user interaction. It should include CVE-2026-0047, because critical Framework privilege-escalation vulnerabilities matter greatly in chained scenarios. It should include CVE-2025-48631, a critical DoS in System, and the 2026-03-05 critical kernel and hypervisor issues such as CVE-2026-0037 and CVE-2026-0038. This is not to dilute focus from the exploited Qualcomm flaw. It is to prevent the common mistake of treating one exploited CVE as if it exists outside the rest of the month’s attack surface. (Android Open Source Project)
For mobile red teams and mobile security engineers, the lesson is broader still. Targeted Android compromise often benefits from chain composition. One flaw gets attention because it is flagged as exploited. Another flaw matters because it creates privilege movement, stability, or stealth. Even when we do not know the exact chain in a given campaign, defenders should plan with chain logic in mind. That means patching the full relevant bulletin level, not just chasing a single CVE badge. (Android Open Source Project)
Why This Matters to Enterprises Outside Traditional Mobile Security
Many organizations still treat phones as communication accessories rather than security-critical endpoints. That mindset is outdated.
Modern Android devices are identity hubs, approval devices, executive briefing consoles, deal-room clients, MFA brokers, and incident communications terminals. In many companies they also hold access to internal documentation, customer conversations, privileged chat groups, code alerts, SaaS admin dashboards, and sometimes even remote management systems. If a targeted attacker compromises the right Android phone, the goal may not be to own Android for its own sake. The goal may be to pivot into accounts, conversations, approvals, or secrets that the phone mediates. (Karanlık Okuma)
That is why CVE-2026-21385 should interest not just mobile defenders, but identity teams, enterprise security leadership, insider-risk teams, and incident responders. The question is not merely “Can this bug crash or corrupt a device?” The question is “What trust does the device carry on behalf of the organization?” For high-value personnel, the answer is often “a lot more than we are comfortable admitting.” (Android Open Source Project)
A Sensible Risk Statement for Leadership
If you need one paragraph for a CISO or VP, it should sound like this:
CVE-2026-21385 is a Qualcomm Android memory-corruption vulnerability disclosed in March 2026, included in Android’s 2026-03-05 patch level, and flagged by Google as possibly under limited, targeted exploitation. CISA has added it to the KEV catalog. Although the public record does not disclose a full exploit chain, the combination of confirmed exploitation activity, broad Qualcomm ecosystem exposure, and Android patch fragmentation makes this an urgent enterprise mobile risk. We should prioritize patch verification to 2026-03-05 or later, focus first on high-value and high-privilege users, and treat this as both a vulnerability response and a mobile trust-management issue. (Android Open Source Project)
That is strong without being theatrical. It is precise without being timid. Most importantly, every core clause in that statement is defensible from the primary sources. (NVD)
Where Penligent Naturally Fits
In practice, the hardest part of CVE response is rarely reading the bulletin. It is proving that your response actually happened. For a vulnerability like CVE-2026-21385, security teams need more than awareness. They need a repeatable workflow that maps devices and exposure, validates whether patch-level or downstream controls changed as intended, and produces evidence that can be handed to leadership, compliance teams, and customers. That is the kind of gap where an AI-assisted security validation platform can be useful: not as a magic “patch Android for me” button, but as an automation layer for exposure analysis, verification logic, and evidence generation tied to real environments. Penligent’s own recent Hacking Labs content has framed this well in adjacent CVE response scenarios, especially around turning “scope, prioritize, patch, verify, document” into a consistent operational loop rather than a one-off scramble. (Penligent)
For teams already managing mixed assets, Penligent is most naturally relevant at the verification and reporting layer. The platform is not the patch source of truth for Android OEM rollouts, but it can help security teams operationalize post-disclosure work: identify exposed assets, validate configuration and risk-reduction changes, structure investigation steps, and generate artifacts that make remediation measurable. That is a more honest and more useful role than forcing a generic product plug into a mobile zero-day story. Where the fit is strongest is not hype. It is evidence. (Penligent)
Final Take
CVE-2026-21385 is one of those vulnerabilities that teaches an old lesson in a modern setting: attackers do not care whether defenders think a bug “looks local.” They care whether it is useful.
The official record already gives security teams enough reason to move. Google says there are indications of limited, targeted exploitation. Qualcomm classifies the flaw as a memory-corruption issue tied to alignment during memory allocation. NVD preserves the High score and CWE-190 mapping. CISA elevated it into KEV almost immediately. The Android bulletin places it in the 2026-03-05 patch level, which means organizations have an explicit remediation target. That is enough to justify urgent inventory, patch verification, risk-tiered outreach, and temporary tightening of mobile security posture for sensitive users. (Android Open Source Project)
The teams that will handle this well are not the ones that publish the loudest Slack message. They are the ones that can answer four concrete questions within days: which devices were exposed, which users mattered most, which patch level is now verified, and what evidence proves the risk window closed. In Android security, that is the difference between “we saw the news” and “we actually reduced the risk.” (Android Open Source Project)
Daha Fazla Okuma
For the primary record, start with the Android March 2026 Security Bulletin and the NVD entry, which together establish the exploitation note, patch-level guidance, description, CVSS, and CWE mapping. (Android Open Source Project)
For the U.S. government urgency signal, review the CISA KEV addition and the associated NVD references showing the March 3, 2026 inclusion and March 24 federal due date. (CISA)
For contemporaneous reporting that captures how the broader security community interpreted the event, the CyberScoop, SecurityWeek, Dark Reading, and Help Net Security coverage are useful because they consistently emphasize the Android March 2026 patch context, the Qualcomm component risk, the broad chipset surface, and the targeted-exploitation signal. (CyberScoop)