Why “CVE-2026-20127 PoC” Became a Top Search Overnight
When defenders search cve-2026-20127 Poc, they’re rarely looking for curiosity material. They’re usually in one of these situations:
- They run Cisco SD-WAN and need to know whether they’re already compromised.
- Their SD-WAN control plane is reachable from the internet and leadership wants an answer in hours, not weeks.
- They saw the words “authentication bypass,” “CVSS 10.0,” and “active exploitation,” and they want a concrete way to validate exposure and confirm remediation.
This vulnerability sits in the worst possible place: the control and management plane of SD-WAN. That’s not “a box you patch when you get time.” It’s the plane that determines how sites connect, how policies are enforced, and how traffic is routed.
Multiple public reports and advisories describe exploitation in the wild and a post-compromise playbook focused on long-term access. (Blog Cisco Talos)
Executive summary, the shortest version that’s still accurate
- What it is: Anulación de la autenticación in Cisco Catalyst SD-WAN Controller y Manager that can allow an unauthenticated remote attacker to obtain administrative privileges. (NVD)
- Gravedad: CVSS 10.0 y explotado activamente. (Cisco)
- Threat actor: Cisco Talos tracks related exploitation/post-compromise under UAT-8616. (Blog Cisco Talos)
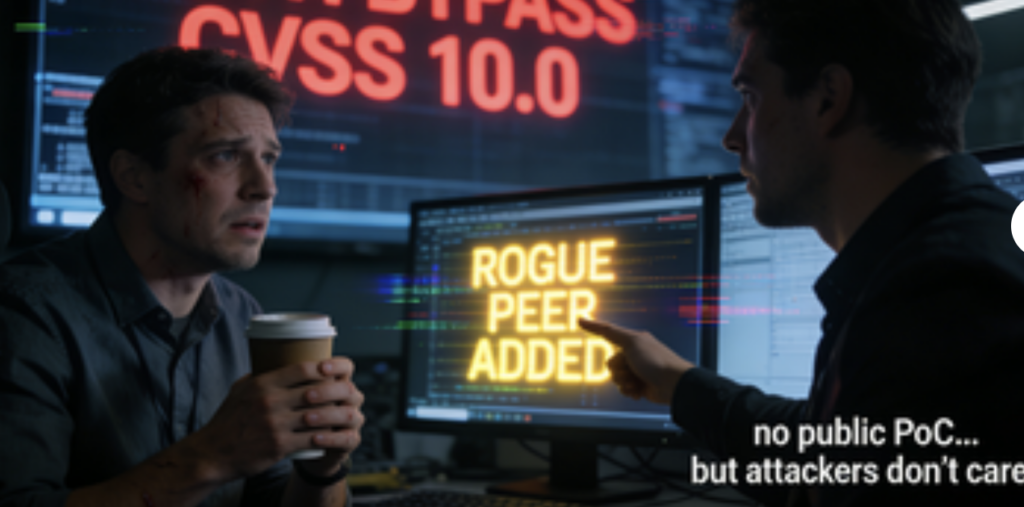
- Attack pattern (high level): exploit → add a rogue peer → interact inside the restricted management plane → pursue persistence and potentially escalate privileges (including techniques like downgrade-then-escalate described in hunt guidance).
- PoC status: at least one public advisory explicitly notes no publicly available PoC code at the time of writing (this can change fast). (eSentire)
- What to do: patch to fixed releases, reduce control-plane exposure, and hunt for compromise signals (peering events, auth.log anomalies, downgrades, suspicious accounts/keys, log clearing). (Noticias Hacker)
Affected products and deployments, what’s actually in scope
Impacted components
- Cisco Catalyst SD-WAN Controller (formerly vSmart)
- Cisco Catalyst SD-WAN Manager (formerly vManage) (NVD)
Deployment types called out as affected
Public reporting summarizes that the issue affects multiple deployment models, including on-prem and Cisco-hosted options (including FedRAMP environments). (Noticias Hacker)
Why control plane exposure matters
One widely repeated warning in coverage is simple: controllers exposed to the internet are at risk. (Noticias Hacker)
In SD-WAN, “at risk” doesn’t mean “someone can read a banner.” It means an attacker may gain a trust position in the fabric.
What makes CVE-2026-20127 so dangerous, a trust-boundary failure in plain English
The vulnerability is described as a failure in the peering authentication mechanism that can allow authentication bypass and admin privileges. (NVD)
That wording hides the operational reality:
- Peering is how SD-WAN components decide who is “one of us.”
- If an attacker can bypass that, they can potentially introduce a component that the fabric treats as trusted.
- Once trusted, actions that should be “internal-only” can start happening from the outside.
This is why defenders saw the term rogue peer show up immediately across multiple reports: it’s a concise way to describe “a non-legitimate participant that becomes trusted anyway.”
The observed attack chain, reconstructed from public hunt guidance
Publicly released hunt guidance and incident summaries repeatedly focus on a playbook that prioritizes stealth and persistence:
- Initial access via the authentication bypass
- Add a rogue peer to gain trusted positioning in the SD-WAN management/control plane
- Interact within the management plane (including access patterns that enable administrative actions) (U.S. Department of War)
- Persistence tactics: local accounts that mimic legitimate users; SSH authorized keys; startup script modification (U.S. Department of War)
- Defense evasion: log/history clearing, including removal under
/var/logand shell history patterns (U.S. Department of War) - Privilege escalation path noted in public reporting: downgrade to a vulnerable version and exploit a known local privilege escalation CVE (CVE-2022-20775) before restoring the original version. (U.S. Department of War)
The important point isn’t the exact sequence in every environment. It’s that control-plane compromise creates options: persistence, stealth, configuration manipulation, and a platform for additional exploitation.
Fixed versions and patch targets, what you should treat as “done”
A practical problem in fast-moving incidents is confusion around versioning. Public reporting consolidates fixed releases by train. The following fixed versions are listed in a widely circulated incident writeup:
- Para 20.9: fixed in 20.9.8.2
- Para 20.11: fixed in 20.12.6.1
- Para 20.12.5: fixed in 20.12.5.3
- Para 20.12.6: fixed in 20.12.6.1
- Para 20.13 / 20.14 / 20.15: fixed in 20.15.4.2
- Para 20.16 / 20.18: fixed in 20.18.2.1
- “Prior to 20.9.1”: migrate to a fixed release (Noticias Hacker)
Rapid7’s response writeup also highlights upgrade guidance at the train level (example: 20.11 → 20.12.6.1+). (Rápido7)
Patch reality check
Patching answers “is the known vulnerability still present,” but it doesn’t answer “were we already compromised last month.” That’s why public guidance pairs patching with hunting and hardening.
CVE-2026-20127 PoC, what’s public, what’s not, and what you can safely do
PoC availability, the state of play
At least one public advisory states that there was no publicly available PoC exploit code at the time of writing, while warning that this could change quickly. (eSentire)
That aligns with what typically happens in high-profile network edge bugs under active exploitation: attackers often have private tooling first, defenders get partial behavioral visibility, and public PoCs may appear later.
What this guide will not provide
This article will no provide weaponized exploit code, step-by-step intrusion instructions, or anything that meaningfully lowers the barrier to attacking real systems.
What this guide will provide instead, the defender version of “PoC”
You still need something concrete. So below you’ll get:
- Exposure validation: are your control-plane endpoints reachable, and are you running affected trains
- Hunting queries: high-signal log patterns called out in public guidance
- Evidence-based verification: how to confirm you’re patched y not showing the compromise behaviors described publicly
High-signal hunting, what to look for first
A) Unexpected control connection peering events
Public guidance repeatedly says peering events must be validated manually: timestamp vs maintenance windows, source IP legitimacy, peer system IP correctness, and peer type consistency. (Rápido7)
Talos includes a sample peering log entry, and then explains exactly what to validate. (Blog Cisco Talos)
B) auth.log anomalies tied to administrative access
Public reporting recommends auditing /var/log/auth.log for entries like Accepted publickey for vmanage-admin from unknown or unauthorized IPs. (Noticias Hacker)
C) Persistence artifacts
Talos notes indicators such as:
- unauthorized SSH keys for
raízovmanage-admin PermitRootLogin yesensshd_config- suspicious accounts created/used/deleted, paired with missing histories
- abnormally small or empty log files
- evidence of log truncation and clearing across syslog, wtmp, lastlog, cli-history, bash_history (Blog Cisco Talos)
D) Downgrade and reboot patterns
Public reporting describes an observed pattern: downgrade to a vulnerable version, exploit a local privilege escalation (CVE-2022-20775), then restore the prior version. (Noticias Hacker)
Practical detection, code and queries you can deploy without “exploitation”
Table, quick mapping from signal to evidence source
| What you’re trying to detect | Por qué es importante | Where to look | What “good” looks like |
|---|---|---|---|
| Rogue peer / unexpected peering | Core compromise primitive | SD-WAN control connection logs | Peers only from known infra, during change windows (Rápido7) |
| vmanage-admin publickey logins | Privileged foothold | /var/log/auth.log | Only known IPs, tied to real operators (Noticias Hacker) |
| Unauthorized authorized_keys | Durable access | ~/.ssh/authorized_keys | Only managed keys, change-controlled (Blog Cisco Talos) |
| Log clearing / tiny logs | Defense evasion | /var/log, wtmp, lastlog, histories | Normal sizes, continuous history (Blog Cisco Talos) |
| Downgrade then upgrade | Likely privesc workflow | upgrade/downgrade logs, reboot events | Only scheduled upgrades, with tickets (U.S. Department of War) |
1) Simple grep-based triage, fast and surprisingly effective
# 1) Look for suspicious vmanage-admin SSH key usage
sudo grep -R "Accepted publickey for vmanage-admin" /var/log/auth.log*
# 2) Hunt for root logins and session changes
sudo grep -R "root" /var/log/auth.log* | head -n 200
# 3) Identify obvious log truncation signals, tiny or empty logs
sudo find /var/log -type f -size -4k -printf "%p %s bytes\\n" | sort -nk2 | head -n 50
# 4) Quick sweep for authorized_keys that shouldn't exist
sudo find /home -maxdepth 3 -path "*/.ssh/authorized_keys" -print -exec sudo sed -n '1,5p' {} \\;
sudo test -f /home/root/.ssh/authorized_keys && sudo sed -n '1,10p' /home/root/.ssh/authorized_keys
Why these are high-value: Talos explicitly calls out unauthorized keys, root sessions, and abnormally small logs as high-fidelity compromise signals. (Blog Cisco Talos)
2) Splunk-style query patterns, adapt to your index names
# Peering events outside maintenance windows, unknown public IPs
index=sdwan ( "control-connection-state-change" OR "peer-type" OR "peer-system-ip" )
| eval hour=strftime(_time, "%H")
| where hour<6 OR hour>20
| stats count values(peer_type) values(peer_system_ip) values(public_ip) by host
# vmanage-admin key-based logins
index=os_linux "Accepted publickey for vmanage-admin"
| stats count values(src_ip) values(user) by host
# Signs of log clearing, sudden drops in log volume
index=os_linux sourcetype=syslog host=*
| timechart span=1h count by host
You’re operationalizing the exact validations called out: timestamp, source IP legitimacy, peer types, correlation patterns. (Rápido7)

3) A safe “PoC-style” validator script, turn peering logs into a review queue
Below is not an exploit. It’s a reviewer: it parses peering events and flags anomalies so humans can validate them, consistent with Talos/Rapid7 guidance. (Rápido7)
import re
from datetime import datetime
PEER_RE = re.compile(
r"control-connection-state-change.*peer-type:(?P<peer_type>\\w+)\\s+"
r"peer-system-ip:(?P<peer_system_ip>[\\d.]+)\\s+public-ip:(?P<public_ip>[\\d.]+)"
)
# Customize these to your environment
KNOWN_PUBLIC_IPS = {"203.0.113.10", "198.51.100.7"} # authorized controller/manager public IPs
KNOWN_SYSTEM_IPS = {"10.10.10.10", "10.10.10.11"} # known system IPs from your inventory
ALLOWED_PEER_TYPES = {"vmanage", "vsmart", "vedge", "vbond"}
MAINTENANCE_HOURS = set(range(0, 24)) - set(range(1, 5)) # example: disallow 01:00-04:59
def suspicious(ts: datetime, peer_type: str, peer_system_ip: str, public_ip: str) -> list[str]:
flags = []
if peer_type not in ALLOWED_PEER_TYPES:
flags.append(f"unexpected peer_type={peer_type}")
if public_ip not in KNOWN_PUBLIC_IPS:
flags.append(f"unknown public_ip={public_ip}")
if peer_system_ip not in KNOWN_SYSTEM_IPS:
flags.append(f"unknown peer_system_ip={peer_system_ip}")
if ts.hour not in MAINTENANCE_HOURS:
flags.append(f"odd hour={ts.hour:02d}")
return flags
def parse_line(line: str):
m = PEER_RE.search(line)
if not m:
return None
# Try to parse syslog timestamp like "Feb 20 22:03:33"
try:
ts = datetime.strptime(line[:15], "%b %d %H:%M:%S").replace(year=datetime.now().year)
except Exception:
ts = datetime.now()
return ts, m.group("peer_type"), m.group("peer_system_ip"), m.group("public_ip")
with open("sdwan_peering.log", "r", errors="ignore") as f:
for line in f:
parsed = parse_line(line)
if not parsed:
continue
ts, peer_type, peer_system_ip, public_ip = parsed
flags = suspicious(ts, peer_type, peer_system_ip, public_ip)
if flags:
print(f"[REVIEW] {ts} {peer_type=} {peer_system_ip=} {public_ip=} flags={flags}")
How to use it:
- Feed it a collected log slice (exported from your SD-WAN logging pipeline).
- Populate
KNOWN_PUBLIC_IPSyKNOWN_SYSTEM_IPSfrom your asset inventory. - Treat output as a human review queue, exactly as public guidance recommends. (Rápido7)
Evidence-based remediation, how to say “we’re good” without bluffing
A defensible closeout statement usually includes three claims, each with evidence:
- We patched to fixed versions Evidence: system version output, package manifest, or manager UI version, mapped to fixed trains. (Noticias Hacker)
- We reduced exposure of the control and management planes Evidence: firewall rules, allowlists, network segmentation notes (including isolating VPN512 and controlling perimeter reachability), and remote syslog forwarding confirmation.
- We hunted for compromise behaviors described in public guidance and found none, or we found and remediated them Evidence: peering events reviewed, auth.log checks, authorized_keys inventory, downgrade/reboot analysis, and log integrity review. (Blog Cisco Talos)
Related CVEs you should understand in the same breath
CVE-2022-20775, the commonly referenced privilege escalation step
Multiple public reports link observed activity to a downgrade-and-escalate flow involving CVE-2022-20775 after initial access, then restoring versions. (Noticias Hacker)
The defensive takeaway is not “memorize this CVE.” It’s: watch for downgrade events, and treat them as incident-grade signals in environments that don’t routinely downgrade.
Other Cisco Catalyst SD-WAN vulnerabilities mentioned in joint advisory context
A joint advisory references additional SD-WAN CVEs in the same family of disclosures (as part of the broader remediation narrative).
This matters because attackers don’t need your environment to be “perfectly vulnerable.” They need one entry point and one follow-on weakness, then they chain.
If you’re running large environments, the hard part is rarely “knowing a CVE exists.” The hard part is:
- proving which targets are exposed
- verifying patch levels across messy inventories
- continuously re-checking after maintenance windows
- keeping evidence that stands up in post-incident review
That’s the niche where an AI-driven automation workflow can help: treat CVE response as a repeatable verification pipeline, not an ad-hoc scramble. If you’re already using automated testing to validate security boundaries, a platform like Penligent can be used to structure “black-box proof” around real assets and produce audit-ready artifacts rather than screenshots and assumptions. (See the Penligent links at the end for related published material.)
Referencias
https://nvd.nist.gov/vuln/detail/CVE-2026-20127 https://www.tenable.com/blog/cve-2026-20127-cisco-catalyst-sd-wan-controllermanager-zero-day-authentication-bypass https://blog.talosintelligence.com/uat-8616-sd-wan/ https://www.rapid7.com/blog/post/etr-critical-cisco-catalyst-vulnerability-exploited-in-the-wild-cve-2026-20127/ https://thehackernews.com/2026/02/cisco-sd-wan-zero-day-cve-2026-20127.html https://media.defense.gov/2026/Feb/25/2003880301/-1/-1/0/CSA_Exploitation_of_SD-WAN_Appliances.PDF https://media.defense.gov/2026/Feb/25/2003880299/-1/-1/0/CISCO_SD-WAN_THREAT_HUNT_GUIDE.PDF https://www.cyber.gc.ca/en/alerts-advisories/al26-004-critical-vulnerability-affecting-cisco-catalyst-sd-wan-cve-2026-20127 https://digital.nhs.uk/cyber-alerts/2026/cc-4748 https://www.penligent.ai/hackinglabs/exploit-db-in-2026-2/ https://www.penligent.ai/hackinglabs/claude-code-security-and-penligent-from-white-box-findings-to-black-box-proof/ https://www.penligent.ai/hackinglabs/cve-2025-4517-the-python-tar-extraction-bug-that-breaks-trust-boundaries-in-real-automation/ https://www.penligent.ai/hackinglabs/technical-deep-dive-exploit-analysis-of-cve-2026-21440-for-ai-security-engineers/ https://www.penligent.ai/hackinglabs/the-rise-of-autonomous-hacking-how-ai-pentest-tools-are-rewriting-security/