If you only skimmed the headlines around CVE-2025-68161, you could walk away with the wrong impression in either direction. Some public writeups framed it like another critical Log4j emergency. Other teams, seeing that it was not an unauthenticated remote code execution bug on the scale of Log4Shell, treated it as background noise. Both reactions miss the point. Public coverage did at times use “critical” language, but Apache, GitHub Advisory, NVD, Snyk, and Tenable all describe the flaw as a medium-severity issue with specific preconditions, not a general-purpose internet-scale RCE. (SiteGuarding)
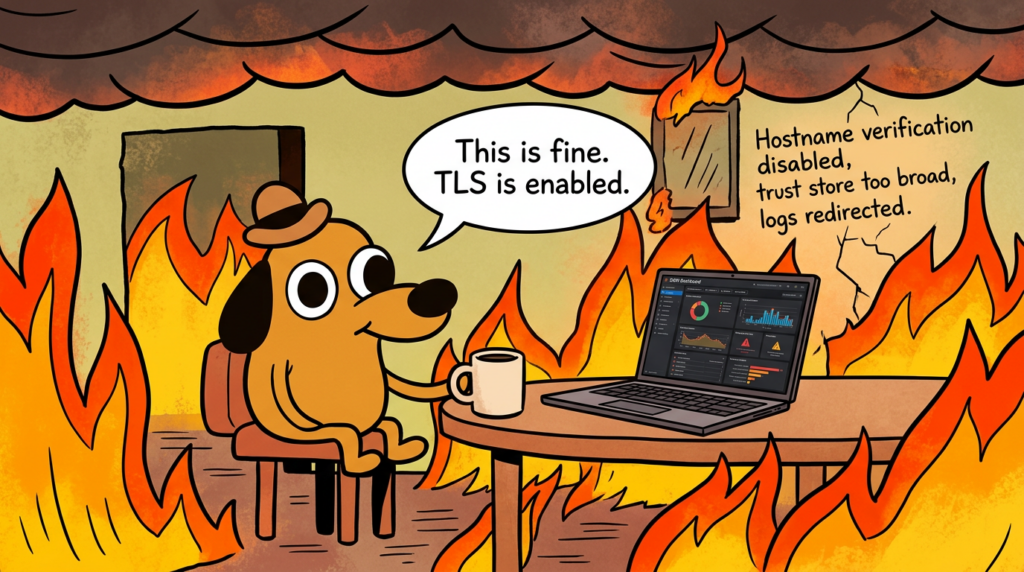
CVE-2025-68161 affects Apache Log4j Core’s Socket Appender. In affected versions, the appender does not properly verify the TLS hostname in the peer certificate, even when the relevant configuration attribute or system property is explicitly set to enable hostname verification. Apache lists affected versions as 2.0-बीटा9 के माध्यम से 2.25.2, के साथ 2.25.3 as the fixed upstream release. NVD shows the CVE published on December 18, 2025, while Apache’s release notes show Log4j 2.25.3 shipped on December 15, 2025 and specifically fixed incorrect handling of hostname verification in SSL/TLS configuration used by Socket Appender. (एनवीडी)
That timing matters. It tells you this was not a vague “theoretical someday” concern. The bug was understood concretely enough to be patched in code before the vulnerability record fully propagated through the downstream ecosystem. The Apache project also credits Samuli Leinonen as the finder and says the issue was reported through the Log4j Bug Bounty Program on YesWeHack, funded by the Sovereign Tech Agency. That is a useful signal that this was a real defect discovered through deliberate security review, not scanner folklore or a vendor-specific packaging oddity. (अपाचे लॉगिंग सेवाएँ)
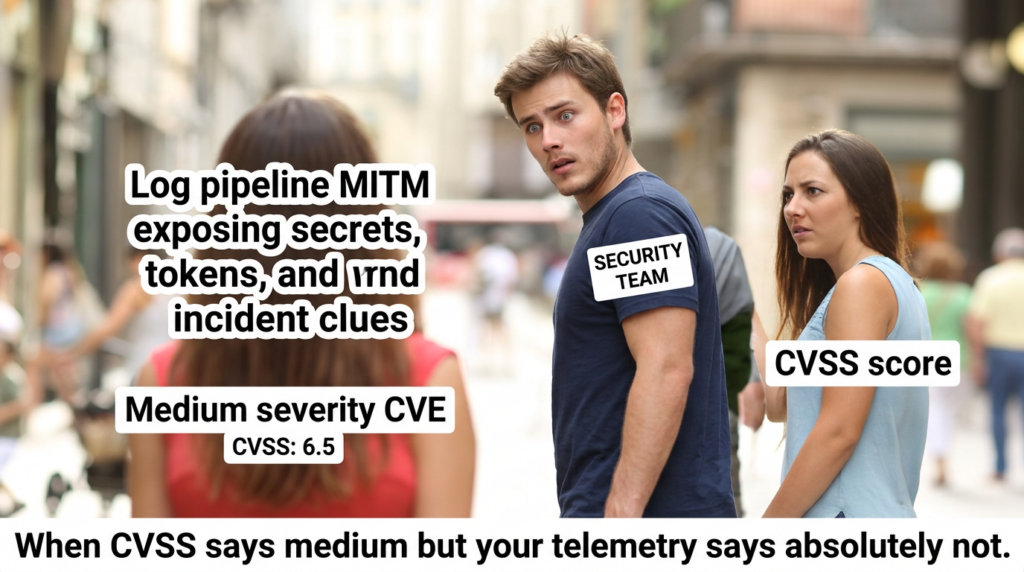
The right way to think about CVE-2025-68161 is not “Is this as bad as Log4Shell?” It is “Do I rely on a remote logging path whose TLS trust assumptions are weaker than I thought?” That question lands directly in the territory of security engineering, cloud platform operations, blue-team telemetry integrity, and application runtime hardening. If your organization forwards logs over TLS to syslog collectors, SIEM shippers, central logging relays, or internal observability hubs, then the bug belongs in a real risk conversation, even if it does not belong in the same severity bucket as CVE-2021-44228. (अपाचे लॉगिंग सेवाएँ)
What CVE-2025-68161 actually is
Apache’s own description is direct. The Socket Appender in Log4j Core versions 2.0-बीटा9 के माध्यम से 2.25.2 does not perform TLS hostname verification of the peer certificate, even when the verifyHostName configuration attribute or the log4j2.sslVerifyHostName system property is set to सच्चा. Apache says this may allow a man-in-the-middle attacker to intercept or redirect log traffic if the attacker can get in the path between the client and the log receiver and can present a certificate issued by a certification authority trusted by the configured trust store or by the default Java trust store. NVD, GitHub Advisory, Snyk, and Tenable all repeat the same core mechanics. (अपाचे लॉगिंग सेवाएँ)
This is a certificate-validation bug, but more specifically it is a hostname-validation bug. The distinction matters. Many engineers hear “TLS is enabled” and mentally translate that to “the endpoint is authenticated.” But TLS only gives you the endpoint identity you verify. If the chain is trusted but the hostname is not actually checked against the certificate, you can still end up talking securely to the wrong server. That is exactly the class of weakness represented by CWE-297, and NVD also maps it to the broader CWE-295 family of improper certificate validation. (एनवीडी)
The Log4j manuals are also useful here because they make clear what the product behavior was supposed to be. In the network appender documentation, the verifyHostName option is documented to compare the hostname in the X.509 certificate to the requested hostname and fail the connection on mismatch. The system-properties documentation separately describes log4j2.sslVerifyHostName as the global control that enables verification of the TLS server name. In other words, the feature existed conceptually and was documented as protective. The CVE exists because that intended protection was not actually taking effect in the vulnerable code path. (अपाचे लॉगिंग सेवाएँ)
Apache’s patch and tests make the remediation path more concrete. In the fixing commit, Log4j sets the endpoint identification algorithm to HTTPS via SSLParameters, and the tests assert that hostname verification should take effect and that the SNI server name is populated for the expected hostname. The release notes for 2.25.3 then summarize this as a fix for incorrect handling of hostname verification in SSL/TLS configuration used by Socket Appender. That is important because it shows this was not merely a documentation adjustment or wording cleanup; the patch materially changed how the socket manager configures TLS verification at runtime. (गिटहब)
Here is the shortest practical snapshot:
| क्षेत्र | मूल्य |
|---|---|
| सीवीई | CVE-2025-68161 |
| प्रभावित घटक | Apache Log4j Core, Socket Appender |
| प्रभावित संस्करण | 2.0-बीटा9 के माध्यम से 2.25.2 |
| Fixed upstream version | 2.25.3 |
| कमजोरी वर्ग | Improper certificate validation, including host mismatch validation |
| प्राथमिक जोखिम | MITM interception or redirection of log traffic |
| गंभीरता | CVSS v4 6.3 medium, CVSS v3.1 4.8 medium |
The table above reflects Apache, NVD, GitHub Advisory, Snyk, and Tenable. (अपाचे लॉगिंग सेवाएँ)

Why this is not another Log4Shell
The fastest way to lose credibility with engineers is to flatten every Log4j CVE into “another Log4Shell.” Apache’s own security page is enough to show why that is wrong. CVE-2021-44228 was the classic Log4Shell vulnerability: JNDI lookup could be exploited to execute arbitrary code loaded from an attacker-controlled LDAP server, Apache scored it at 10.0 critical, and it affected broad ranges of लॉग4जे-कोर. CVE-2021-44832, by contrast, was a JDBC Appender RCE in certain configurations when an attacker had write access to logging configuration, and Apache scored it at 6.6 medium. CVE-2025-68161 sits in a different class again: a man-in-the-middle condition tied to hostname verification in the Socket Appender path. (अपाचे लॉगिंग सेवाएँ)
That comparison is not academic. Log4Shell mattered because an attacker who could influence log messages or parameters could sometimes get arbitrary code execution with almost absurd reach. Apache’s description says exactly that for CVE-2021-44228, and NVD reflects the same basic behavior. CVE-2025-68161 is narrower. It does not hand an attacker code execution simply because they can send a crafted request into a vulnerable app. It requires the target to use the affected remote logging path and requires the attacker to be able to intercept or redirect traffic and satisfy trust-store expectations. That changes both prioritization and validation strategy. (अपाचे लॉगिंग सेवाएँ)
At the same time, “not Log4Shell” does not mean “not important.” Logging traffic often carries data that defenders assume is moving through a trustworthy internal channel. If you break trust in that channel, the blast radius is different from RCE, but still serious: confidentiality loss from log interception, integrity loss through redirection or substitution, and operational confusion if a team believes telemetry is reaching the right place when it is not. CVSS v4 reflects that shape by assigning low confidentiality impact on the vulnerable system and low integrity impact on a subsequent system, not catastrophic availability loss or broad direct compromise. (एनवीडी)
There is another useful nuance here. Apache’s network appender documentation says the TCP and TLS variants write as a stream and do not expect a response from the target destination, and that some events may continue to appear delivered until a SocketException is raised after the target closes the connection. That means the operational model for remote logging is already not a hard, acknowledgment-backed assurance channel. If you combine that with broken hostname verification, the risk is not just “could a packet be read?” It is also “could the system continue behaving as if the right collector is receiving logs while trust is silently misplaced?” (अपाचे लॉगिंग सेवाएँ)
The part most headlines flatten
One of the most interesting things about CVE-2025-68161 is how quickly public framing drifted. Some early articles described it in dramatic “critical vulnerability” language, often emphasizing attacker access to sensitive logs without spending much time on the concrete exploit prerequisites. By contrast, Apache’s official advisory, GitHub Advisory, Snyk, and Tenable all classify it as medium and explicitly call out attack complexity or conditionality. That gap between headline framing and exploit reality is part of why teams mis-triage this kind of bug. (SiteGuarding)
A mature reading is this: the flaw is real, the fix is straightforward, and the environment-specific exploitability is the whole game. If you do not use Socket Appender over TLS, the CVE may exist in the JAR but not in your actual risk path. If you do use it, but only with a tightly scoped private trust root, your exposure is lower than an environment that trusts broad public roots or an overly broad enterprise CA hierarchy. If you use it with hostnames, broad trust roots, and logging traffic that crosses shared or interceptable network zones, the problem becomes materially more interesting. Apache says as much in its alternative mitigation guidance by recommending a private or restricted trust root. (अपाचे लॉगिंग सेवाएँ)
This is also where many scanner-only workflows fall down. Scanners are very good at telling you that a versioned artifact is present. They are much worse at telling you whether the vulnerable code path is configured, reachable, and security-relevant in your runtime. Downstream vendor advisories already show this distinction in practice. Broadcom, for example, says the issue is only relevant when the Log4j2 SocketAppender functionality is used and states that its Workload Automation Agent does not utilize that specific functionality; Omnissa similarly published product impact assessments saying some products were not exploitable in context. That is exactly the lesson defenders should extract: package presence is not the same thing as exposure truth. (Support Portal)
The exact exploit conditions
Apache lays out two explicit conditions for exploitation. First, the attacker must be able to intercept or redirect network traffic between the client and the log receiver. Second, the attacker must be able to present a certificate issued by a certification authority trusted by the Socket Appender’s configured trust store, or by the default Java trust store if no custom trust store is configured. Those are the two anchor points of the whole CVE. Everything else is operational detail around them. (अपाचे लॉगिंग सेवाएँ)
That sounds simple, but each condition breaks into its own engineering questions.
Your application uses Socket Appender or Syslog over TLS
The vulnerable path is not “all of Log4j.” It is Log4j Core’s Socket Appender path when used with TLS. Apache’s documentation says Socket Appender writes to a remote destination over TCP or UDP sockets, and you can optionally secure the communication with TLS. The same documentation says Syslog Appender is a utility plugin built on top of Socket Appender, inheriting the remaining configuration attributes and nested elements from Socket Appender. That means teams using TLS-protected syslog forwarding through Log4j should treat Syslog Appender configurations as squarely in scope. (अपाचे लॉगिंग सेवाएँ)
The documentation also shows the practical configuration shape: a Socket appender with host, port, and nested Ssl configuration, or a Syslog appender using the same Ssl structure. Apache’s examples show 6514 as the default SSL port for Socket Appender and common syslog-over-TLS-style configurations. So when you assess reachability, you are not just hunting for the string SocketAppender; you are hunting for any remote logging config that resolves to Log4j’s socket-based network path with TLS enabled. (अपाचे लॉगिंग सेवाएँ)
The attacker can sit on the path or redirect the path
This requirement is what keeps CVE-2025-68161 from being a broadly sprayable RCE bug. The attacker has to be in a position to intercept or redirect traffic to the remote log receiver. That can mean a classic on-path scenario, but it can also include more subtle network manipulation: DNS-level misdirection, routing or service-discovery mistakes, internal network compromise, trust abuse involving logging relays, or any architecture where the log destination is remote and not strongly bound to a single authenticated endpoint. Apache consistently describes the issue as interception or redirection of log traffic, not code execution. (अपाचे लॉगिंग सेवाएँ)
For defenders, the important takeaway is that remote log shipping is often treated as a “safe backplane.” In reality, it is just another networked control channel. If your apps emit logs over TLS to collectors that live across clusters, across VPCs, across subnets, or across hybrid links, you already have a chain of assumptions: name resolution, routing correctness, trust-root correctness, and endpoint authenticity. CVE-2025-68161 weakens the last of those assumptions in the vulnerable versions.
The certificate still chains to a trusted root
The bug is not “TLS off.” The attacker still needs a certificate that the client will trust. Apache’s advisory is explicit about that. This is why trust-store design matters so much in real impact analysis. If your Socket Appender trusts a broad set of public roots or inherits the default Java trust store without narrowing scope, there are more possible certificates that can satisfy chain validation. Apache’s own mitigation advice is to use a private or restricted trust root, and it explicitly points to NIST SP 800-52 Rev. 2 as an example of established best practice around narrowly scoped trust stores. (अपाचे लॉगिंग सेवाएँ)
This is also why many teams will discover that the most security-relevant fix is not only “upgrade the dependency” but “stop treating log transport trust like a generic outbound HTTPS trust problem.” A dedicated private CA, or a trust store that contains only the CA material necessary for your logging channel, dramatically reduces the universe of certificates that could be abused in a redirection scenario. Apache says this directly, and the mitigation logic is sound even before you patch. (अपाचे लॉगिंग सेवाएँ)
The destination is a hostname, not just an IP literal
One of the most useful technical details lives in the documentation and patch, not the headline summaries. Apache’s network appender manual says hostname verification is only effective when the provided host is not an IP literal and is a valid hostname, citing RFC 6066 and RFC 1035. In the fixing patch, Log4j populates SNI host information only when the host is valid in that sense. That means some teams will “upgrade and still be confused” if their logging configuration points directly at IP literals and they expect hostname verification semantics to save them. Hostname verification protects hostnames. It is not magic identity binding for arbitrary IP endpoints. (अपाचे लॉगिंग सेवाएँ)
That nuance is easy to miss and operationally important. If your remote logging path is configured as 10.0.12.7 instead of something like syslog.prod.internal, then even a patched environment may not be using hostname verification the way your team assumes. In those cases, the remediation conversation has to include service naming and certificate naming discipline, not just version pinning.
What an attacker can really do with this bug
The official language says “intercept or redirect log traffic,” and that is exactly the right place to start. Interception means the wrong party can read the log stream while the application believes it is sending data securely. Redirection means the application can be tricked into sending logs to a different endpoint that still appears acceptable under the broken trust model. The immediate impact shape from the scoring is modest compared with RCE, but the operational consequences can still be ugly. (अपाचे लॉगिंग सेवाएँ)
Consider what commonly lives inside logs in modern Java systems. Even well-run teams end up logging pieces of request context, authentication failures, internal hostnames, stack traces, error identifiers, queue names, service account names, tenant identifiers, trace IDs, database names, file paths, API routes, and sometimes fragments of secrets or tokens that should never have made it there. Mature teams try to reduce that data, but they do not eliminate it. The point is not that every log stream is a pile of crown jewels. It is that log streams are unusually rich in context. They tell an attacker how the system thinks, how it routes, how it fails, and what it trusts.
That makes CVE-2025-68161 particularly relevant for internal attackers, post-compromise lateral movement, insider misuse, and red-team scenarios that focus on telemetry blind spots rather than initial execution. If I can observe or redirect your log stream, I may not own your application process, but I may learn enough about your environment to make later compromise easier. I may also degrade your detection posture by affecting where evidence goes, what collector receives it, and how incident responders reconstruct sequence and scope.
There is also a less glamorous but highly practical point: logs are often part of compliance evidence. They are used in investigations, in audit narratives, in incident timelines, in regulatory response, and in customer-facing postmortems. The confidentiality and integrity of log transport therefore matter well beyond the app team that owns the emitting service. That is one reason Apache’s mitigation guidance emphasizes trust-store hygiene rather than treating the problem as a minor transport nit. (अपाचे लॉगिंग सेवाएँ)
Why log traffic is a high-value target
Security teams often prioritize vulnerabilities by asking whether the bug can turn into a shell. That is a useful instinct, but it can underweight attacks against observability and control-plane data. Remote logging is one of those channels that looks administrative until you inspect what actually moves through it. Apache’s own Socket Appender examples are telling: the documentation frames common use around syslog-style remote collection, structured layouts, and buffered transport over TCP or SSL. That is not debug trivia. That is production telemetry. (अपाचे लॉगिंग सेवाएँ)
Production telemetry has a special value because it compresses application truth. A request may touch three microservices, a queue, a cache, and a database, but the log stream often pulls the most relevant state into one place. A collector that receives those logs sees operational and often security-relevant context in near real time. That is why defenders centralize it. It is also why attackers want it.
In a breach investigation, teams often discover that the first clue was not a packet capture or a crash dump. It was a weird auth failure, an unusual header value, a bad certificate path, a suspicious role assumption, or a stack trace from an edge case the attacker triggered repeatedly. If the channel carrying that evidence is silently redirected or made observable to an unauthorized intermediary, the damage is not theoretical. It is investigative.
This is also where the contrast with Log4Shell becomes useful rather than distracting. Log4Shell taught the industry that a dependency bug in logging infrastructure could become a global intrusion primitive. CVE-2025-68161 teaches a more subtle lesson: even when the bug is not code execution, logging infrastructure still sits on a sensitive trust boundary. That is a different class of pain, but it is still pain. CISA’s long-running Log4j guidance and later advisories on continued Log4Shell exploitation are a reminder that the ecosystem learned the hard way not to dismiss “just logging” as low consequence.
(सीआईएसए)
How to decide whether your environment is truly exposed
The right triage workflow for CVE-2025-68161 is not difficult, but it does require discipline. You need to answer four questions in order.
First, do you have a vulnerable copy of लॉग4जे-कोर in the runtime or build path. Second, are you actually using Socket Appender or Syslog over TLS in a live configuration. Third, does the app connect to a remote log destination through a trust model broad enough to make redirection plausible. Fourth, is the logging destination configured as a hostname that hostname verification can meaningfully validate. If you cannot answer all four, your ticket is not actually triaged yet.
A useful mental model is this:
| Finding | What it means | What it does not mean |
|---|---|---|
Vulnerable लॉग4जे-कोर version present | The dependency needs assessment or patching | Immediate active exploitability |
| Socket or Syslog appender present | The relevant code path may be configured | TLS is necessarily enabled |
| TLS enabled with remote host | The CVE becomes more relevant | Hostname verification is necessarily working |
| Broad trust roots in use | Redirection risk is more meaningful | The path is definitely exploited |
| Hostname endpoint configured | Verification can be meaningful after fix | The environment is already safe if still unpatched |
This is the kind of bug where an engineer who understands runtime truth will outperform a purely severity-driven process every time.
Step 1, inventory every copy of log4j-core
Start with version truth. Apache says the vulnerable range is everything from 2.0-बीटा9 के माध्यम से 2.25.2, के साथ 2.25.3 as the upstream fix. Snyk and GitHub Advisory say the same, and NVD reflects the same version boundaries. (अपाचे लॉगिंग सेवाएँ)
In Maven, Gradle, container, and shaded-JAR environments, I would begin with something like this:
# Maven
mvn -q dependency:tree | grep -i "log4j-core"
# Gradle
./gradlew dependencies --configuration runtimeClasspath | grep -i "log4j-core"
# Search inside built artifacts
find . -type f \( -name "*.jar" -o -name "*.war" -o -name "*.ear" \) -print0 \
| xargs -0 sh -c 'for f; do jar tf "$f" 2>/dev/null | grep -q "log4j-core" && echo "$f"; done' sh
# Container or filesystem SBOM style checks
syft dir:. 2>/dev/null | grep -i "log4j-core"
Those commands are not special. The point is to identify every runtime-bearing copy, including transitive and bundled artifacts.
If your environment uses distro packages rather than direct Maven coordinates, pay attention to backports. Debian LTS fixed bullseye in package version 2.17.1-1~deb11u2, and SUSE shipped package-level security updates in its own maintenance stream. That means “not literally 2.25.3” does not automatically mean “still vulnerable” when the platform vendor has backported the fix. Engineers who miss this point often generate a lot of false escalation churn. (Debian Mailing Lists)
Step 2, find the runtime configuration path
Once you know the dependency is present, you need to find whether the application actually uses the affected network logging features. Apache’s docs show the exact families to search for: Socket, Syslog, nested Ssl, TrustStore, KeyStore, and the hostname-verification controls. Syslog inherits from Socket Appender, so it counts. (अपाचे लॉगिंग सेवाएँ)
A quick first pass can look like this:
find . -type f \( \
-name "log4j2.xml" -o -name "log4j2.json" -o -name "log4j2.yaml" -o -name "log4j2.yml" -o -name "log4j2.properties" \
-o -name "*.xml" -o -name "*.json" -o -name "*.yaml" -o -name "*.yml" -o -name "*.properties" \
\) -print0 | xargs -0 egrep -n \
"Socket|Syslog|Ssl|TrustStore|KeyStore|verifyHostName|log4j2\.sslVerifyHostName|Rfc5424Layout"
What you are looking for is not just whether Log4j exists, but whether the application is configured to send logs to a remote destination over TLS. A local file appender plus a vulnerable JAR is a patching problem. A live remote socket logging path plus a vulnerable JAR is a patching problem with a concrete exposure story.
If you want a safer runtime check from inside a Java application, a simple introspection snippet can help enumerate configured appenders:
import org.apache.logging.log4j.LogManager;
import org.apache.logging.log4j.core.LoggerContext;
import org.apache.logging.log4j.core.config.Configuration;
import org.apache.logging.log4j.core.Appender;
public class Log4jAppenderCheck {
public static void main(String[] args) {
LoggerContext ctx = (LoggerContext) LogManager.getContext(false);
Configuration cfg = ctx.getConfiguration();
for (Appender appender : cfg.getAppenders().values()) {
System.out.println(appender.getName() + " -> " + appender.getClass().getName());
}
}
}
That will not tell you the whole trust story, but it is enough to distinguish “we only write to local files” from “we really do have a socket-backed logging path in production.”
Step 3, verify whether remote logging over TLS is live
A static config file is not always the whole truth. Profiles change. Environment overrides exist. Some services ship with multiple appenders and only activate one at runtime. Apache’s docs show both local and remote patterns, and the system-properties page makes clear that SSL and trust-store behavior can be influenced globally. So the next step is to verify what is actually live in the deployed environment. (अपाचे लॉगिंग सेवाएँ)
That usually means checking:
- the resolved host and port for the remote collector
- whether the protocol is really
SSLor effectively plainTCP - whether the trust store is custom or default
- whether the app is using a hostname or an IP literal
- whether the collector is internal-only or transits shared network zones
I know you generally prefer paragraph form, but for this one the five checks are the real checklist. They are the difference between triage and theater.
A useful thing to remember is that Apache documents default port 6514 for the SSL case and 4560 for TCP in the Socket Appender path. So if you are inventorying live connections or firewall rules, those patterns can help you spot candidate flows quickly, especially in legacy Java estates where nobody remembers how the logs are shipped anymore. (अपाचे लॉगिंग सेवाएँ)
Step 4, inspect the trust model
This step is where many teams finally discover whether the CVE is merely present or truly uncomfortable.
Apache’s workaround guidance is explicit: if you cannot upgrade immediately, configure Socket Appender to use a private or restricted trust root. Apache cites NIST guidance for keeping trust stores scoped to the intended communication domain. The reason is obvious once you think about the exploit chain. A broken hostname check is far less useful to an attacker if the only certificates the client will accept are from a private CA dedicated to that exact logging ecosystem. A broken hostname check is much more useful if the client trusts a broad public root set or a sprawling enterprise CA environment with many issuance paths. (अपाचे लॉगिंग सेवाएँ)
So ask very boring questions:
What CA certificates are in the trust store.
Why are they there.
Are they shared across unrelated services.
Does the logging channel have its own PKI or just inherit whatever the JVM trusts.
Can another internal service plausibly obtain a certificate chaining to the same root.
These are not glamorous questions, but they are where the real exposure lives.
Step 5, test the failure mode in staging
After patching, the goal is not only “new version deployed.” The goal is “bad certificate and wrong hostname actually fail closed.” Apache’s patch uses HTTPS endpoint identification and SNI handling, and the documentation says hostname mismatch should fail the connection. That is what you should verify in a staging environment. (गिटहब)
The clean way to validate is not to build a red-team stunt. It is to point the application at a staging receiver whose certificate chain is trusted but whose certificate name does not match the configured hostname, then confirm the connection is rejected after the fix. Also test the normal path with the correct certificate and a valid hostname. That gives you evidence that the patch is doing the thing your policy says it should do.
Remediation, upgrade first, trust-store hardening second
The primary remediation is simple: upgrade org.apache.logging.log4j:log4j-core को 2.25.3 or later. Apache, GitHub Advisory, Snyk, Tenable, and NVD all align on that. (अपाचे लॉगिंग सेवाएँ)
For Maven:
<dependencyManagement>
<dependencies>
<dependency>
<groupId>org.apache.logging.log4j</groupId>
<artifactId>log4j-bom</artifactId>
<version>2.25.3</version>
<type>pom</type>
<scope>import</scope>
</dependency>
</dependencies>
</dependencyManagement>
<dependencies>
<dependency>
<groupId>org.apache.logging.log4j</groupId>
<artifactId>log4j-core</artifactId>
</dependency>
</dependencies>
For Gradle:
dependencies {
implementation platform("org.apache.logging.log4j:log4j-bom:2.25.3")
implementation "org.apache.logging.log4j:log4j-core"
}
Apache’s components documentation also assumes use of the Log4j BOM in normal dependency management. (अपाचे लॉगिंग सेवाएँ)
If you are pinned to distro packages, use the vendor-supported patched package rather than forcing an out-of-band JAR swap unless you know exactly what you are doing. Debian LTS and SUSE both published updates for CVE-2025-68161 in their own package streams. That is especially important in enterprise environments where the vendor package may include supportable backports rather than upstream version strings that look “newer” to a generic scanner. (Debian Mailing Lists)
If you cannot upgrade immediately, Apache’s fallback is to reduce risk by carefully restricting the trust store used by Socket Appender. That means private or enterprise-specific trust roots only, not a generic “trust everything the JVM already trusts” posture. In practice, I would pair that with three operational moves: keep the collector on a dedicated internal name, move the logging path onto network segments with tighter control, and eliminate IP-literal destinations if you expect hostname verification to be meaningful after the patch. Apache’s docs and patch behavior support all three recommendations. (अपाचे लॉगिंग सेवाएँ)
A defensive Log4j configuration pattern should therefore look more like this:
<Socket name="SYSLOG"
host="syslog.prod.internal"
port="6514"
protocol="SSL">
<Rfc5424Layout appName="payments-api"
facility="DAEMON"
id="Log4j"
newLineEscape="\n"/>
<Ssl verifyHostName="true">
<TrustStore location="/etc/app/logging-truststore.p12"
type="PKCS12"
passwordEnvironmentVariable="LOGGING_TRUSTSTORE_PASSWORD"/>
</Ssl>
</Socket>
The important ideas are not the exact attribute order. They are the hostname-based endpoint, TLS enabled, hostname verification enabled, and a dedicated trust store instead of a broad ambient default. Those design choices follow directly from Apache’s manual and mitigation guidance. (अपाचे लॉगिंग सेवाएँ)
One more practical recommendation: after patching, re-run the same SCA and config discovery workflow you used for initial triage. Teams often fix the direct dependency and miss a shaded copy in a legacy worker, a vendor agent, a desktop admin tool, or a packaged appliance. The amount of downstream advisory traffic for CVE-2025-68161 from IBM, Broadcom, Omnissa, OpenText, F5, and others shows how often Log4j rides along inside bigger products. (आईबीएम)
Related CVEs security engineers should keep in the same mental model
When security teams talk about “the Log4j family,” they are often mixing bugs that look similar only because they share a library name. That is not good enough. The useful comparison is by exploit precondition and failure mode.
| सीवीई | Core bug class | Typical precondition | Severity picture | यह क्यों मायने रखती है |
|---|---|---|---|---|
| CVE-2025-68161 | Broken TLS hostname verification in Socket Appender | Remote logging over TLS, attacker can intercept or redirect traffic, certificate chains to trusted root | मध्यम | Telemetry confidentiality and integrity risk |
| CVE-2021-44228 | JNDI lookup arbitrary code execution | Attacker controls log message or parameters in vulnerable setup | आलोचनात्मक | Canonical Log4Shell RCE |
| CVE-2021-44832 | JDBC Appender RCE in certain configurations | Attacker can modify logging configuration and abuse JNDI URI | मध्यम | Config-controlled RCE, narrower but still serious |
| CVE-2021-45046 | Incomplete fix to Log4Shell in certain non-default configs | Specific MDC and Pattern Layout conditions | आलोचनात्मक | Follow-on exploitability after initial patching confusion |
The table above is drawn from Apache’s security documentation and NVD-linked records summarized there. (अपाचे लॉगिंग सेवाएँ)
There is also a fresher ecosystem point worth making. Apache’s current security page includes newer 2025 logging-project issues such as CVE-2025-54813 and CVE-2025-54812, but those affect Log4cxx, not Log4j Core. One is an improper escaping issue in JSONLayout, the other is improper HTML escaping in HTMLLayout. They are real bugs, but they are different projects and different failure classes. Engineers who work too quickly often collapse all “Apache Logging” issues into one remediation blob. That is exactly how bad prioritization happens. (अपाचे लॉगिंग सेवाएँ)
The best mental model is not “all Log4j issues are existential” and not “this one is medium so it can wait forever.” It is “treat logging vulnerabilities as a cluster, then separate them by code path, preconditions, and actual consequence.” That is the lesson many teams learned painfully after Log4Shell and its follow-on CVEs. Apache’s own security history around CVE-2021-44228, CVE-2021-45046, CVE-2021-45105, and CVE-2021-44832 makes that evolution clear. (अपाचे लॉगिंग सेवाएँ)
What this means for bug bounty hunters, red teamers, and defenders
For bug bounty hunters and red-team operators, CVE-2025-68161 is a useful reminder that not every valuable finding ends in a shell. In mature targets, the hard part is often proving trust-boundary failure in a way that has operational meaning. If you can demonstrate that a remote logging path is configured over TLS, that hostname validation is broken in the deployed version, that the trust store is too broad, and that sensitive log traffic crosses a realistic interception boundary, you have a strong security story even without an RCE. That kind of work is closer to real security engineering than screenshot-chasing a version banner.
For defenders, the lesson is symmetrical. A scanner hit is not enough, but neither is dismissing the issue because the CVSS is not catastrophic. The real task is proving whether the vulnerable channel is live and what would be exposed if trust in that channel fails. On a good team, that conversation spans application engineering, platform networking, PKI ownership, SIEM operations, and incident response. That cross-functional nature is why bugs like this often sit unresolved longer than they should.
It is also why I would not over-index on EPSS alone. Public scoring sources currently reflect relatively low mass-exploitation likelihood compared with historic Log4j catastrophe scenarios. Snyk shows EPSS around 0.1% at the time of access, and Tenable shows a similarly low value. That is useful context, but it should not become an excuse to skip validation in environments where the preconditions are genuinely present. Low mass exploitation probability does not mean low consequence in the one estate where the architecture lines up badly. (VulnGuide)
This is one of those CVEs where a proof-oriented workflow matters more than a scanner-only workflow. Penligent describes itself as an AI-powered penetration testing tool, and recent Penligent materials repeatedly frame the hard part of modern vulnerability work as validation, exploitability truth, and evidence-backed remediation rather than raw CVE enumeration. That framing fits CVE-2025-68161 unusually well, because the central question is not “Can my scanner see an old JAR?” It is “Can I prove whether this remote logging path is actually configured, reachable, and relevant to the security boundary I care about?” (पेनलिजेंट)
Penligent’s own Log4Shell-related writing is also relevant as background reading because it treats logging-library exposure as a cluster problem rather than a single-ID checkbox. That is the right mindset here too. For CVE-2025-68161, the best workflow is the same general pattern: identify the dependency, trace the real configuration path, validate the security assumption that is supposed to protect the channel, and then produce remediation evidence that engineering teams can defend later. (पेनलिजेंट)
अधिक जानकारी
- NVD, CVE-2025-68161 (एनवीडी)
- Apache Logging Services, Security advisory for CVE-2025-68161 (अपाचे लॉगिंग सेवाएँ)
- Apache Log4j release notes, version 2.25.3 (अपाचे लॉगिंग सेवाएँ)
- Apache Log4j network appender manual (अपाचे लॉगिंग सेवाएँ)
- Apache Log4j system properties, log4j2.sslVerifyHostName (अपाचे लॉगिंग सेवाएँ)
- GitHub Advisory, GHSA-vc5p-v9hr-52mj (गिटहब)
- Apache fix pull request, PR 4002 (गिटहब)
- Openwall disclosure thread (openwall.com)
- Debian LTS advisory for apache-log4j2 (Debian Mailing Lists)
- SUSE security update for log4j (SUSE)
- CISA Log4j guidance entry point (सीआईएसए)
- Log4Shell is the New SQLi, A Modern Retrospective on CVE-2021-44228 for the AI Era (पेनलिजेंट)
- Log4Shell CVE Still Matters in 2026 — What CVE-2021-44228 Taught Us About Dependency RCE, Detection, and Proof-Based Remediation (पेनलिजेंट)
- ExploitDB, What Public Exploit Code Really Tells You About Exposure (पेनलिजेंट)
- एआई पेंटस्ट टूल, 2026 में वास्तविक स्वचालित आक्रमण कैसा दिखता है (पेनलिजेंट)
- 2026 में पेंटस्ट एआई टूल्स — क्या वास्तव में काम करता है, क्या विफल होता है (पेनलिजेंट)