Why people search “claude code remote control” and what actually matters
إذا قمت بالبحث “claude code remote control”, you’re likely trying to answer one of these questions:
- Does this turn my laptop into a remotely controlled machine if I enable it?
- Can an attacker hijack my Claude session from the cloud?
- Is the risk mainly Anthropic, or mainly my repo and my tooling?
- What should security teams do before developers enable it company-wide?
Remote Control is not a traditional remote desktop tool. According to Anthropic’s own documentation, Remote Control connects the Claude web/mobile interface to a Claude Code process running on your machine, and “the web and mobile interfaces are just a window into that local session.” (Claude)
That single design choice is the whole security story:
- Your code execution stays local.
- Your filesystem access stays local.
- Your MCP servers and local tools stay available.
- Your “small” mistakes—approving the wrong command, trusting the wrong repo, enabling the wrong MCP server—also stay local, with local consequences.
Remote Control doesn’t magically create new vulnerabilities by itself. But it changes behavior و amplifies impact: it makes it easier to keep going from a phone, while the thing you’re controlling is a highly capable agent that can read files, run commands, call tools, and make network requests. Anthropic explicitly frames Claude Code’s model as permission-based with user approval for actions such as command execution, and it also calls out prompt injection and untrusted content risks. (Claude)
So the right question is not “Is Remote Control secure?” The right question is:
What happens when a powerful local execution agent becomes reachable from more places, with more distractions, and with more opportunities to rubber-stamp prompts?
To ground that threat model in reality, we need to connect Remote Control to what the security community just learned about Claude Code’s repo-driven attack surface.
How Claude Code Remote Control works, in security-relevant terms
Anthropic’s Remote Control docs describe a workflow that looks like this:
- You start a Remote Control session from your terminal (or from an existing session).
- Your Claude Code process keeps running locally.
- You connect from another device using a session URL/QR code.
- Anthropic routes messages between the web/mobile client and your local session over TLS. (Claude)
Key security properties Anthropic claims (and that matter to defenders):
- No inbound ports: your local session makes outbound HTTPS requests only. (Claude)
- TLS transport: traffic travels through the Anthropic API over TLS. (Claude)
- Short-lived credentials: multiple short-lived credentials, scoped and expiring independently. (Claude)
- Sandboxing is optional: the Remote Control command supports
-sandbox/-no-sandbox, and sandboxing is off by default (per docs). (Claude)
That last point is where security teams should lean in.
Remote Control makes the agent more accessible. If the agent is not sandboxed, then “accessible” also means “capable” in the full sense of your developer environment: reading local files, invoking tools, reaching internal services, and touching credentials the developer can access. Anthropic’s security model is explicit that Claude Code only has the permissions you grant, and that users are responsible for reviewing commands. (Claude)
In practice, modern engineering teams don’t fail because they don’t know that approvals matter. They fail because approvals become routine.
Remote Control increases the number of contexts where approvals happen:
- on a phone between meetings
- on a laptop tethered to a flaky hotspot
- on a browser session during travel
- in any moment where attention is fragmented
And that’s before we even talk about untrusted repositories.

The threat model shift: from “running untrusted code” to “opening untrusted projects”
In February 2026, Check Point published research showing that Claude Code’s repo-level configuration can be abused to trigger command execution and credential exposure when developers clone/open malicious projects. (Check Point Research)
The Hacker News summary captures the new model in one line: the risk extends to opening untrusted projects, because configuration mechanisms and automation layers can become execution paths. (أخبار القراصنة)
Why this matters for Remote Control:
Remote Control doesn’t need to introduce a brand-new exploit to create real risk. It only needs to increase the probability that a developer:
- opens a repo they shouldn’t trust yet
- misses a trust prompt nuance
- approves a command they wouldn’t approve on a focused workstation
- enables a project MCP server “just to make it work”
- ignores a subtle configuration change because they’re “just continuing a session”
Remote Control is a force multiplier for human factors—especially when the tooling itself is designed to be fast and helpful.
The Claude Code findings that matter most for “Remote Control” risk
The most important “high-CTR” terms you’ll see in coverage around this topic—because they are concrete, alarming, and operational—cluster around:
- تنفيذ التعليمات البرمجية عن بُعد (RCE)
- API key exfiltration
- untrusted repositories
- Hooks و MCP servers
- CVE-2025-59536 و CVE-2026-21852
These themes are consistently emphasized across The Hacker News coverage and Check Point’s write-up. (أخبار القراصنة)
Here’s what’s worth taking away—without turning this into an exploitation guide.
1) Repo-controlled configuration is an execution surface, not “just settings”
Check Point notes that Claude Code supports project-level configuration in .claude/settings.json, checked into the repository to ensure consistent behavior for teams. That convenience creates a supply-chain-shaped risk: anyone who can modify that file in a repo can attempt to influence what Claude does. (Check Point Research)
This is the core mental model change security teams should enforce:
Treat AI-agent project configuration like build scripts or CI workflows: it can execute behavior.
2) Hooks and lifecycle automation increase the blast radius of “just opening” a project
The Hacker News describes a class of issues where untrusted project hooks could lead to code execution under certain conditions, and it frames the broader lesson: automation layers are becoming part of the execution layer. (أخبار القراصنة)
Check Point’s research similarly frames Hooks as deterministic commands executed at lifecycle points—useful for formatting and compliance, but also a potential avenue for abuse in an untrusted repo context. (Check Point Research)
Even if specific bugs are patched, the architectural lesson persists: lifecycle triggers are where “no one is looking.”
3) MCP server auto-enablement turns “tooling” into a supply chain
Claude Code’s official security documentation is explicit that Anthropic does not manage or audit MCP servers and encourages organizations to write their own or use trusted providers. (Claude)
The Hacker News summary also highlights a scenario where repository-defined configuration could override user approval for MCP interactions by toggling an option enabling project MCP servers. (أخبار القراصنة)
Remote Control doesn’t change MCP risk; it changes how quickly and casually people may enable it.
4) API traffic redirection and “early requests” are the quiet data-leak path
The Hacker News notes Anthropic’s advisory for CVE-2026-21852, describing how a malicious repo could set an environment value (e.g., ANTHROPIC_BASE_URL) so that Claude Code issues API requests before the trust prompt, potentially leaking API keys. (أخبار القراصنة)
Check Point’s report goes deeper on observing requests and the reality that initialization can involve sending repository context (like file names and recent commit messages) as part of the session bootstrap. (Check Point Research)
This matters operationally because it reframes “trust prompts” as not always being the first line of defense. Your defense should assume:
- some traffic happens early
- some context is sent by design
- misdirection or proxying can cause unintended disclosure
Remote Control’s concrete risk surface
Let’s translate all of that into a practical checklist. The goal is not to fear-monger. The goal is to help a security team decide what to control.
Risk 1: Account compromise becomes execution compromise
Remote Control sessions are reachable from web/mobile surfaces. If an attacker gains access to the developer’s Claude account session on a phone or browser (phishing, stolen session tokens, compromised device, malicious browser extension), the attacker may not need direct laptop access to influence what the local agent does.
Remote Control’s design uses short-lived credentials and TLS, per Anthropic. (Claude)
But your threat model should assume the weak link is endpoint identity and session integrity, not transport encryption.
Controls
- Enforce strong authentication on the Claude account layer (SSO where supported, phishing-resistant MFA where possible).
- Treat phone/browser as privileged endpoints if Remote Control is enabled.
- Restrict where Remote Control can be used (managed devices only) via policy if you’re an enterprise.
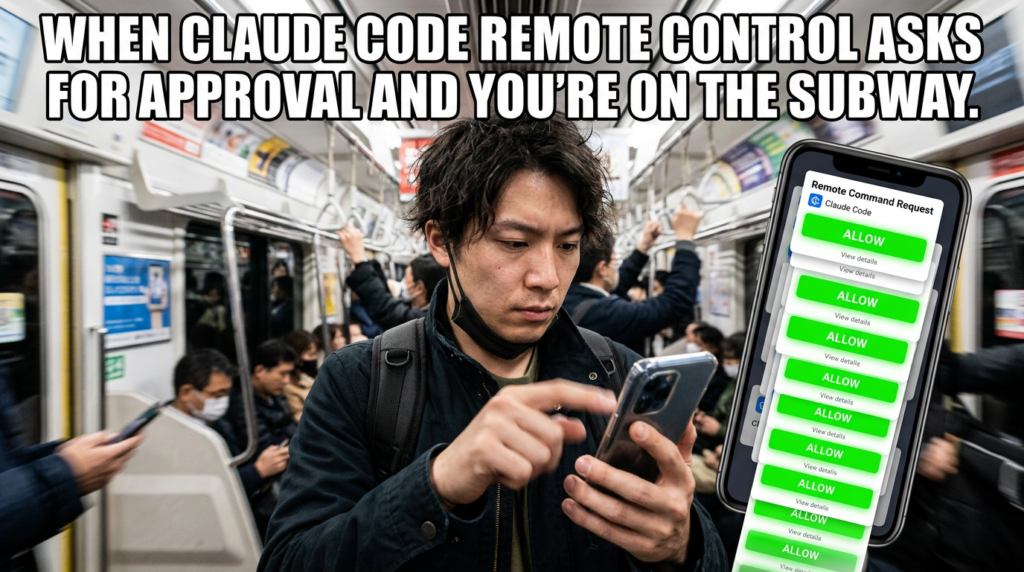
Risk 2: Approval fatigue gets worse when approvals move to a phone
Claude Code’s model relies on users reviewing commands before approval. (Claude)
That’s reasonable—until approvals become muscle memory.
Remote Control is designed to let you keep going while moving. (Claude)
In the real world, “keep going while moving” correlates strongly with “approve quickly.”
Controls
- Default to sandboxed Remote Control sessions where feasible (because sandboxing is off by default). (Claude)
- Require stricter approvals for network and shell actions (no “allow forever” for risky classes).
- Provide a “high risk action” rubric developers can actually follow.
Risk 3: Untrusted repo + agentic tooling = supply chain at the workflow layer
Check Point’s central message is that malicious repositories can weaponize project configuration to trigger execution and credential theft—issues were patched, but the lesson is architectural. (Check Point Research)
Remote Control increases the probability that a developer opens a repo “just to look” and continues from mobile.
Controls
- Add automated preflight checks when entering a repo (see code examples below).
- Block or quarantine repos containing risky AI-agent config patterns until reviewed.
- Separate “browsing repos” from “running agent sessions” via isolated environments.
Risk 4: MCP supply chain and tool impersonation
Claude Code supports MCP servers and emphasizes trust and permissions, but also states Anthropic doesn’t audit MCP servers. (Claude)
That means you own the MCP supply chain.
Controls
- Maintain an internal allowlist of MCP servers and pin versions/hashes where possible.
- Prefer internal MCP servers with code review and provenance.
- Disallow project-defined MCP auto-enable in sensitive repos.
Risk 5: Data exfiltration through “legitimate” network calls
Even when no exploit is present, an agent can leak data through:
- logs
- artifact uploads
- webhook calls
- “helpful” debugging requests to external endpoints
- misconfigured proxies or base URLs
Anthropic documents that Remote Control uses the same TLS transport as other sessions, and notes Remote Control differs from cloud execution (no cloud VM sandbox). (Claude)
So network egress and secrets hygiene are on you.
Controls
- Egress restrict: domain allowlists, deny-by-default outbound from the agent environment.
- Secrets isolation: don’t keep production tokens in dev shells; use scoped, short-lived credentials.
- Detect base URL / proxy changes as high severity events.
A practical table: threat scenarios vs controls
| السيناريو | Likely impact | Why Remote Control increases probability | Prevent | Detect | Respond |
|---|---|---|---|---|---|
| Developer continues session from phone on public Wi-Fi | Session compromise → local command execution | Mobile context + weak network hygiene | Managed devices, strong auth, sandbox sessions | Unusual login/device, session anomalies | Kill sessions, rotate keys, incident review |
Malicious repo adds .claude/settings.json hooks | Command execution, local compromise | “Just open it quickly” becomes “run it” | Repo preflight checks, isolate untrusted repos | Config diffs, suspicious lifecycle events | Quarantine device, forensics, revoke creds |
| Repo manipulates MCP settings / auto-enable | Tool execution, data access, exfiltration | Convenience encourages enabling tools fast | MCP allowlist, disable project auto-enable | New MCP server registrations | Disable server, audit access, rotate tokens |
| Base URL / proxy redirection for API calls | API key leakage, traffic interception | Remote continuation reduces scrutiny | Lock down env vars, policy checks | Detect ANTHROPIC_BASE_URL changes | Rotate keys, review outbound traffic |
| Prompt injection in project docs/issues | Dangerous actions approved | Distraction increases susceptibility | Guardrails, training, sandbox + deny network | Command risk scoring | Roll back changes, postmortem |
Grounding for this table: Claude Code’s security model (permissions, prompt injection safeguards, MCP guidance, Remote Control differences) and Check Point/The Hacker News findings about repo-based configuration abuse and API key exposure. (Claude)
Code: a safe “repo preflight” scanner for Claude Code / MCP config
The goal here is simple: before a developer runs Claude Code (or continues it via Remote Control) inside a repository, scan for risky patterns and require an explicit human review.
Below is a defensive example. It does لا exploit anything. It just flags configuration that should not be trusted by default.
#!/usr/bin/env python3
import json
import os
import sys
from pathlib import Path
RISKY_FILES = [
Path(".claude") / "settings.json",
Path(".mcp.json"),
]
RISKY_KEYS = {
# High-risk toggles and patterns (examples based on public discussion of repo-level settings)
"enableAllProjectMcpServers": "Project MCP auto-enable increases supply-chain risk.",
"hooks": "Hooks can execute lifecycle commands; treat as code.",
"ANTHROPIC_BASE_URL": "Base URL redirection can risk credential leakage/traffic interception.",
}
def load_json(path: Path):
try:
return json.loads(path.read_text(encoding="utf-8"))
except Exception as e:
return {"__parse_error__": str(e)}
def find_keys(obj, prefix=""):
hits = []
if isinstance(obj, dict):
for k, v in obj.items():
p = f"{prefix}.{k}" if prefix else k
if k in RISKY_KEYS:
hits.append((p, RISKY_KEYS[k], v))
hits.extend(find_keys(v, p))
elif isinstance(obj, list):
for i, v in enumerate(obj):
p = f"{prefix}[{i}]"
hits.extend(find_keys(v, p))
return hits
def main():
repo_root = Path.cwd()
findings = []
for rel in RISKY_FILES:
path = repo_root / rel
if path.exists():
data = load_json(path)
hits = find_keys(data)
findings.append((str(rel), data.get("__parse_error__"), hits))
if not findings:
print("No Claude/MCP config files found. Proceed normally.")
return 0
print("=== Repo Preflight: Claude Code / MCP Risk Scan ===")
exit_code = 0
for fname, parse_error, hits in findings:
print(f"\\nFile: {fname}")
if parse_error:
print(f" ! JSON parse error: {parse_error}")
exit_code = 2
continue
if not hits:
print(" ✓ No flagged keys found (still review manually).")
continue
exit_code = 1
for path, rationale, value in hits:
print(f" ! Flag: {path}")
print(f" Reason: {rationale}")
print(f" Value: {repr(value)[:200]}")
print("\\nDecision: If any flags exist, do NOT start/continue Claude Code here until reviewed.")
return exit_code
if __name__ == "__main__":
sys.exit(main())
How to use it safely
- Run it automatically in a pre-commit hook, a
make preflighttarget, or your shell profile when entering a repo directory. - If it flags anything, treat the repo like an untrusted build pipeline until reviewed.
This aligns with the core lesson from Check Point: repo configuration is an attack surface, and opening a project can become a compromise event. (Check Point Research)
CI guardrail: block risky agent config from merging
A lot of orgs already gate Terraform changes, GitHub Actions, and CI scripts. Do the same for AI-agent configuration.
name: Block risky Claude/MCP config
on:
pull_request:
branches: [ "main", "master" ]
jobs:
scan:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- name: Scan Claude/MCP config
run: |
python3 - << 'PY'
import json, sys
from pathlib import Path
files = [Path(".claude/settings.json"), Path(".mcp.json")]
risky = ["enableAllProjectMcpServers", "hooks", "ANTHROPIC_BASE_URL"]
def load(p):
return json.loads(p.read_text(encoding="utf-8"))
def walk(x):
if isinstance(x, dict):
for k,v in x.items():
yield k,v
yield from walk(v)
elif isinstance(x, list):
for v in x:
yield from walk(v)
flagged = []
for f in files:
if f.exists():
data = load(f)
for k,v in walk(data):
if k in risky:
flagged.append((str(f), k, v))
if flagged:
print("Blocked: risky Claude/MCP configuration detected:")
for f,k,v in flagged:
print(f" - {f}: {k} = {repr(v)[:120]}")
sys.exit(1)
print("OK: no risky keys detected (still review changes).")
PY
This doesn’t claim to be perfect. It’s a practical baseline that makes the “repo configuration is execution surface” principle enforceable.
Enterprise-grade controls that actually work
Here’s a set of controls that map cleanly to how Claude Code is described by Anthropic and what Check Point demonstrated.
1) Make sandboxing the default for Remote Control sessions
Remote Control supports sandboxing flags, and Anthropic documents that Remote Control differs from cloud execution (which uses isolated VMs). (Claude)
So if you want cloud-like isolation while staying local, you need to supply it.
Practical options:
- devcontainers
- dedicated VM for agentic tooling
- a separate “AI workstation” with restricted credentials
- OS-level sandbox + outbound network policy
2) Restrict outbound network access for the agent environment
Anthropic notes network request approval defaults, but your enterprise should still enforce network boundaries at the system level. (Claude)
Use:
- deny-by-default egress
- allowlists for package registries and approved APIs
- DNS logging for anomaly detection
3) Treat MCP like a software supply chain
Because Anthropic does not audit MCP servers, you must. (Claude)
Minimum viable governance:
- internal catalog of approved MCP servers
- code owner reviews for MCP configuration changes
- “no project auto-enable” in sensitive repos
- pin versions, require provenance
4) Protect against prompt injection as a workflow problem
Anthropic’s security docs explicitly discuss prompt injection and safeguards, but no safeguard replaces workflow hygiene. (Claude)
Practical workflow rules:
- never paste untrusted content into Claude Code with execution permissions
- treat repo docs/issues as untrusted input
- require “read-only first pass” on untrusted repos
Where CVEs fit, and which ones matter here
The most directly relevant CVEs in this story are the ones tied to Claude Code’s repo/config attack surface:
- CVE-2025-59536 — described in public reporting as a code injection issue allowing arbitrary shell command execution under certain project initialization/trust conditions. (أخبار القراصنة)
- CVE-2026-21852 — described as an information disclosure issue where malicious repo configuration could cause API requests before trust prompts and potentially leak API keys / redirect traffic. (أخبار القراصنة)
The deeper reason to include these is not “because they’re scary.” It’s because they demonstrate an evergreen class of risk:
AI agent configuration and project metadata can become exploit-adjacent execution paths.
If you want a broader industry parallel (without claiming they’re the same bug), high-impact supply-chain incidents like the XZ Utils backdoor debate in 2024 taught the same organizational lesson: build inputs, dependencies, and tooling layers deserve the same rigor as production code because compromise often starts upstream. (Claude)
Claude Code (and Remote Control) live inside the developer execution bubble: repo context, code edits, local tools, and local command execution. That’s valuable for fixing code quickly.
But security programs fail when they stop at “the code looks fixed” and never prove whether the deployed system is still exposed. This is where a black-box, outside-in validation layer is operationally different from code review.
If you’re using Claude Code Security to identify risky flows and patch direction, بنليجنت can be used after the patch to validate exposure against a real staging environment: confirm whether the vulnerability is actually reachable, whether compensating controls work, and whether the fix holds under realistic inputs. Penligent’s own write-up frames this as “white-box findings to black-box proof.” (بنليجنت)
A second practical use: Remote Control increases the chance that developers run more tasks from more places. Penligent can help security teams shift validation left و keep a record of what was tested, what was verified, and what changed—so security leadership isn’t guessing which fixes were actually proven in an environment that attackers would see.
That’s not a replacement for secure-by-default agent governance. It’s a complementary control: prove the boundary, don’t assume it.
Remote Control is not a classic “remote admin” backdoor. Anthropic’s docs say it doesn’t open inbound ports and routes messages over TLS with short-lived, scoped credentials. (Claude)
But Remote Control does turn Claude Code into something that deserves a stronger governance posture:
- It makes a powerful local execution surface reachable from more contexts.
- It increases approval fatigue risk.
- It amplifies the operational impact of repo-based configuration and MCP supply chain issues—exactly the category of problems Check Point highlighted in its Claude Code research. (Check Point Research)
If you’re rolling it out, treat it like privileged tooling:
- isolate it
- sandbox it
- restrict egress
- gate repo configuration changes
- audit MCP
- rotate secrets aggressively
- and assume “opening a project” is now part of your supply-chain threat model
Links
Anthropic Claude Code Docs — Remote Control: https://code.claude.com/docs/en/remote-control Anthropic Claude Code Docs — Security model and best practices: https://code.claude.com/docs/en/security The Hacker News — Claude Code flaws, CVE-2025-59536 and CVE-2026-21852 coverage: https://thehackernews.com/2026/02/claude-code-flaws-allow-remote-code.html Check Point Research — “Caught in the Hook” technical report: https://research.checkpoint.com/2026/rce-and-api-token-exfiltration-through-claude-code-project-files-cve-2025-59536/ Dark Reading — High-level impact summary for developer risk: https://www.darkreading.com/application-security/flaws-claude-code-developer-machines-risk Claude Code Remote Control security risks — local session becomes a remote interface: https://www.penligent.ai/hackinglabs/claude-code-remote-control-security-risks-when-your-local-session-becomes-a-remote-interface/ Claude Code project files became an RCE and API key exfiltration path — what the Check Point findings change: https://www.penligent.ai/hackinglabs/claude-code-project-files-became-an-rce-and-api-key-exfiltration-path-what-the-check-point-findings-change-for-ai-coding-assistants/ Claude Code Security and Penligent — From White-Box Findings to Black-Box Proof: https://www.penligent.ai/hackinglabs/claude-code-security-and-penligent-from-white-box-findings-to-black-box-proof/ Kali Linux + Claude via MCP — execution boundary discussion: https://www.penligent.ai/hackinglabs/kali-linux-claude-via-mcp-is-cool-but-its-the-wrong-default-for-real-pentesting-teams/ Kali LLM, Claude Desktop, and the new execution boundary in offensive security: https://www.penligent.ai/hackinglabs/kali-llm-claude-desktop-and-the-new-execution-boundary-in-offensive-security/